Search for person "Alexander Böhm" returned 144 results
61 min
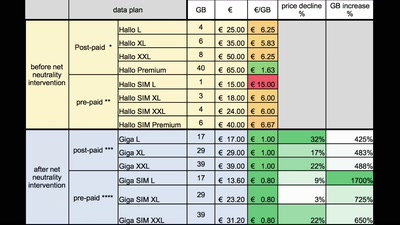
Netzpolitik in Österreich
Ein Jahresrückblick aus dem Land der Datenberge

60 min
Building a high throughput low-latency PCIe based SDR
Lessons learnt implementing PCIe on FPGA for XTRX Software…
60 min
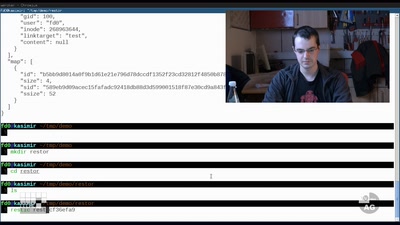
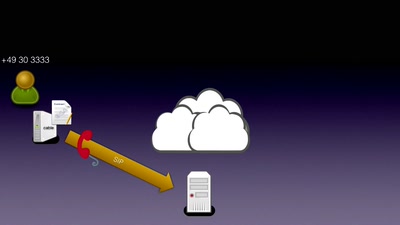
Beyond your cable modem
How not to do DOCSIS networks
140 min
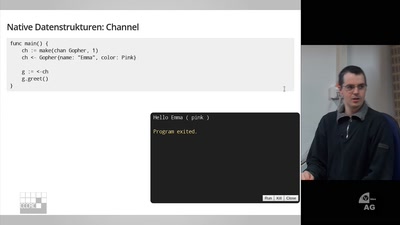
Von Taschenratten und Typen
Die Programmiersprache Go
28 min
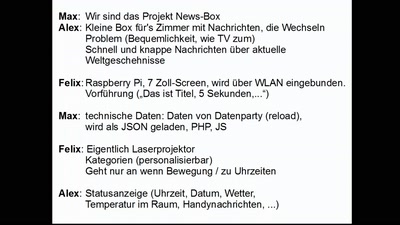
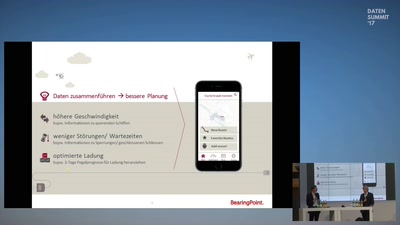
Data-Run: Mobilitätskonzepte mit offenen Daten umsetzen
Die drei Gewinner des BMVI Data Runs stellen ihre Projekte…
55 min
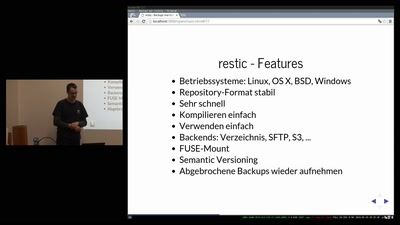
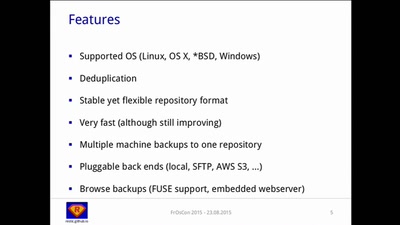
A Solution to the Backup Inconvenience
Fast, Secure and Efficient Backups with "restic"

65 min
Hochverfügbare Firewalls mit Keepalived und Conntrackd
Übernahme von Verbindungsverlust

60 min
Pflanzenhacken richtig
Einblicke in die Weizenzüchtung
65 min
PicoLisp Application Development
Interactive development of PicoLisp database applications
55 min
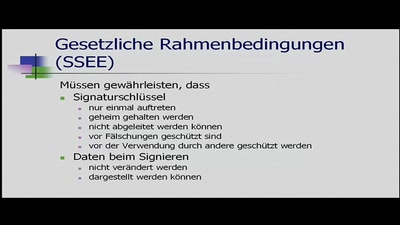
Ein Mittelsmannangriff auf ein digitales Signiergerät
Bachelorarbeit Informatik Uni Kiel SS 2011
56 min