Search for "ar3itrary" returned 269 results
63 min
goto fail;
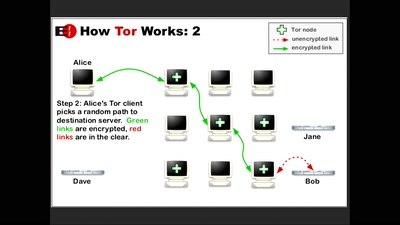
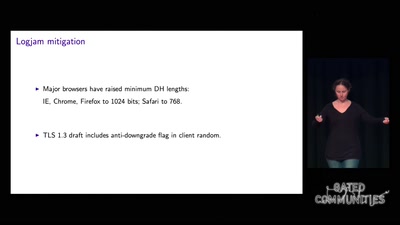
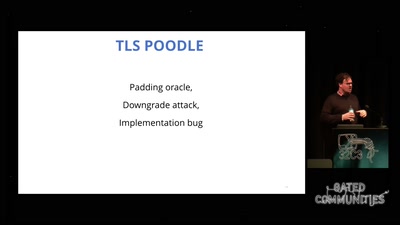
exploring two decades of transport layer insecurity
63 min
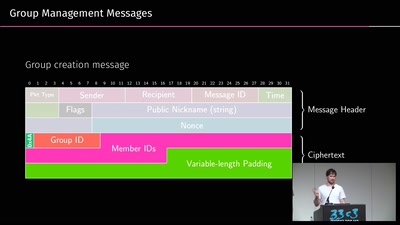
A look into the Mobile Messaging Black Box
A gentle introduction to mobile messaging and subsequent…
43 min
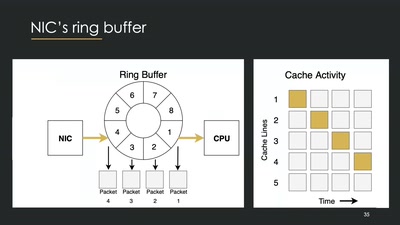
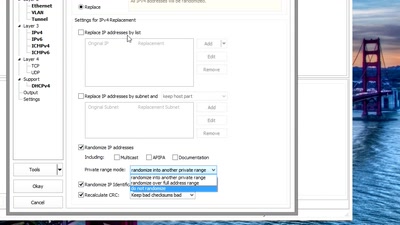
Sanitizing PCAPs
Fun and games until someone uses IPv6 or TCP

45 min
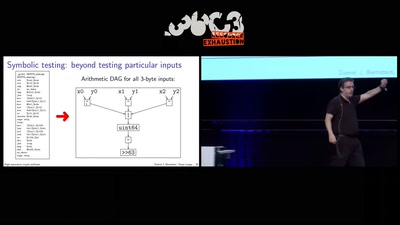
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
61 min
Rocket Kitten: Advanced Off-the-Shelf Targeted Attacks Against Nation States
A Deep Technical Analysis
59 min
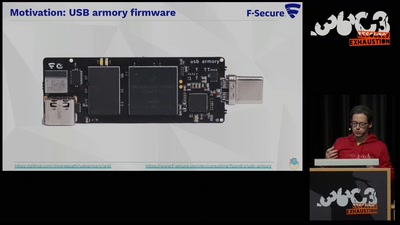
TamaGo - bare metal Go framework for ARM SoCs.
Reducing the attack surface with pure embedded Go.
59 min
The Surveillance State limited by acts of courage and conscience
An update on the fate of the Snowden Refugees
61 min
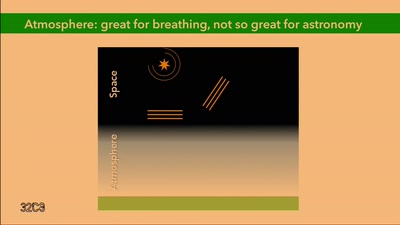
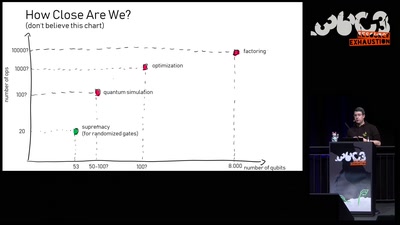
Quantum Computing: Are we there yet?
An introduction to quantum computing and a review of the…
42 min
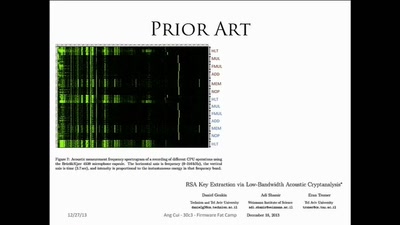
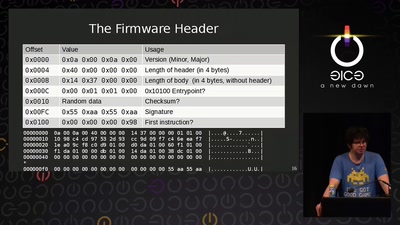
Firmware Fat Camp
Embedded Security Using Binary Autotomy
60 min
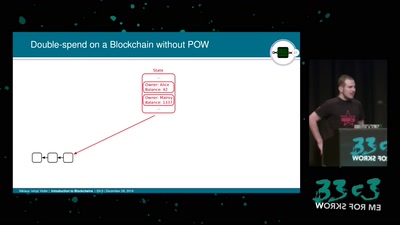
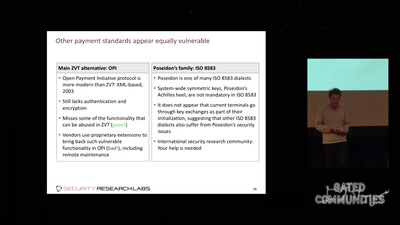
Shopshifting
The potential for payment system abuse
54 min
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
62 min
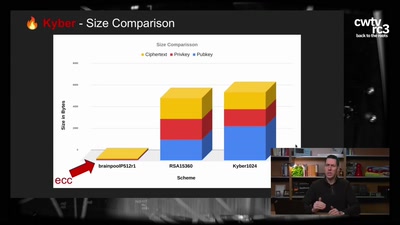
Kyber and Post-Quantum Crypto
How does it work?
53 min