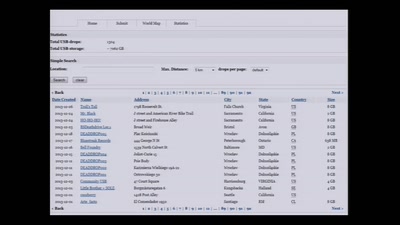
Search for "luky" returned 271 results
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
55 min
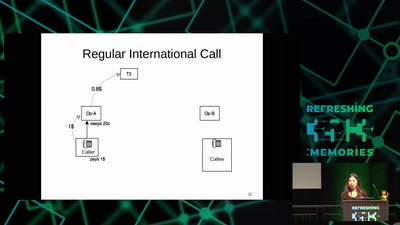
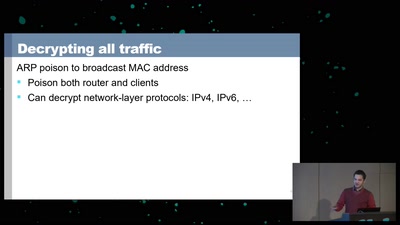
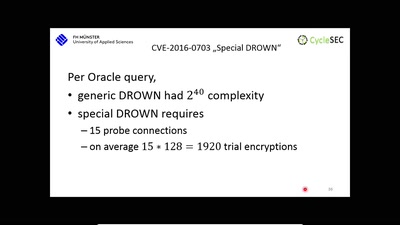
The DROWN Attack
Breaking TLS using SSLv2
62 min
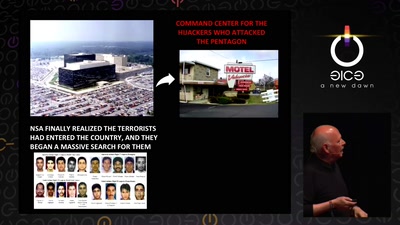
Tell no-one
A century of secret deals between the NSA and the telecom…
60 min
APT Reports and OPSEC Evolution, or: These are not the APT reports you are looking for
How advanced threat actors learn and change with innovation…
58 min
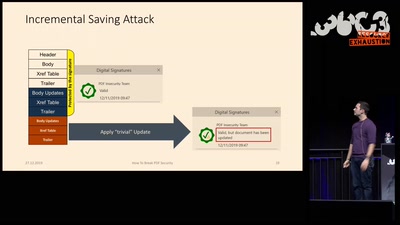
How to Break PDFs
Breaking PDF Encryption and PDF Signatures
57 min
A New Dark Age
Turbulence, Big Data, AI, Fake News, and Peak Knowledge
61 min
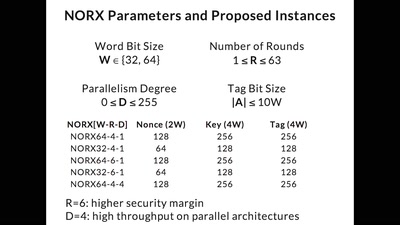
CAESAR and NORX
Developing the Future of Authenticated Encryption

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
58 min
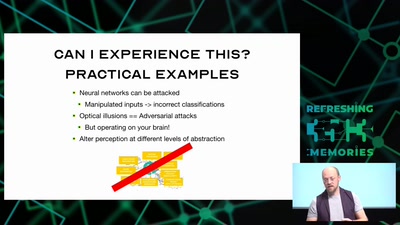
Hacking how we see
A way to fix lazy eye?
57 min