Search for "Arne" returned 4196 results
55 min
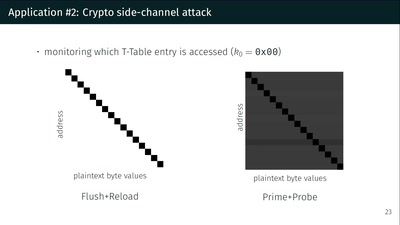
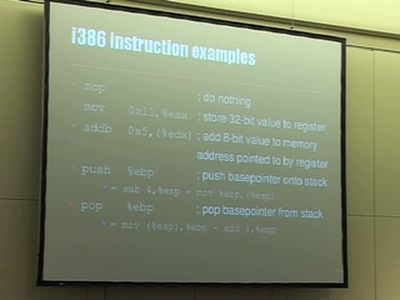
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
26 min
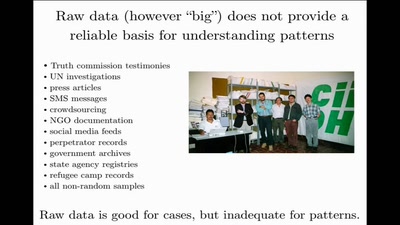
Data Mining for Good
Using random sampling, entity resolution, communications…

59 min
Hacking EU funding for a decentralizing FOSS project
Understanding and adapting EU legal guidelines from a FOSS…
49 min
A short political history of acoustics
For whom, and to do what, the science of sound was…
47 min
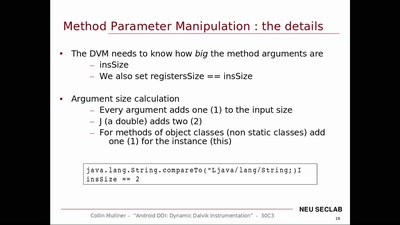
Android DDI
Dynamic Dalvik Instrumentation of Android Applications and…
20 min
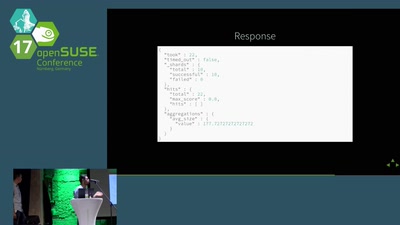
Ceph, ELK & opensuse
This talk will be held by Denys Kondratenko and Abhishek…
57 min
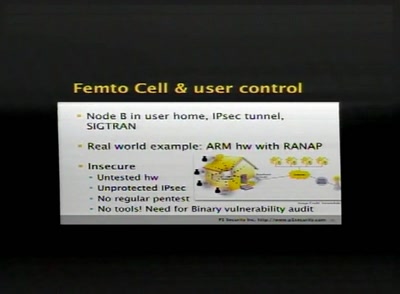
SCCP hacking, attacking the SS7 & SIGTRAN applications one step further and mapping the…
Back to the good old Blue Box?
38 min
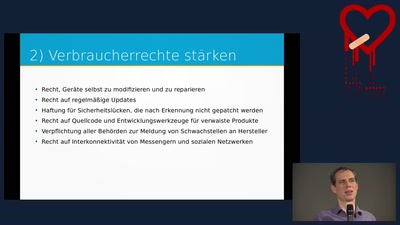
IT-Sicherheit für Verbraucher stärken
Entwicklung eines IT-Sicherheitsbewertungssystems für…

33 min
Gone in 60 Milliseconds
Intrusion and Exfiltration in Server-less Architectures

69 min
Implementing flexible page layouts with Drupal
Using the PHPTemplate engine and the Content Construction…
55 min
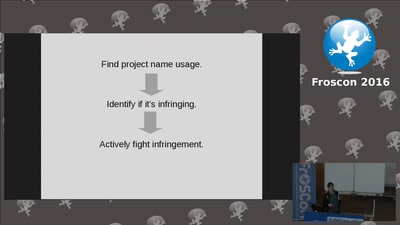
Open source is just about the source, isn't it?
Stuff your open source project needs to care about that…

55 min
The Gospel of IRMA
Attribute Based Credentials in Practice
55 min
Our daily job: hacking the law
The key elements of policy hacking
60 min
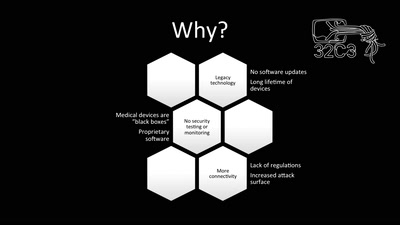
Unpatchable
Living with a vulnerable implanted device
59 min