Search for "wose" returned 908 results

31 min
A Tale of Two Leaks:
How Hackers Breached the Great Firewall of China
53 min
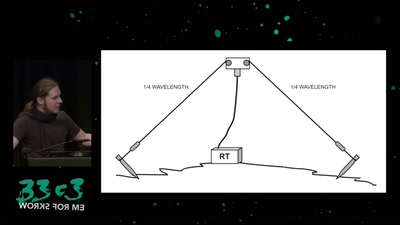
Surveilling the surveillers
About military RF communication surveillance and other…

24 min
The Four Wars
Terror, whistleblowers, drugs, internet
55 min
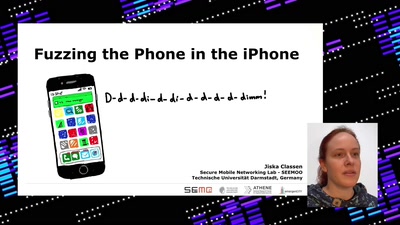
Fuzzing the phone in the iPhone
D-d-d-di-di-d-d-di-d-di-d-di-d-dimm!
40 min
A year of surveillance in France: a short satirical tale by La Quadrature du Net
From the so-called Country of human rights to a…
63 min
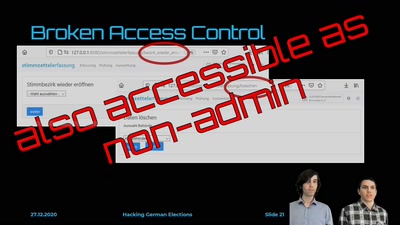
Hacking German Elections
Insecure Electronic Vote Counting - How It Returned and Why…
31 min
Access To Bodies
Ein Leitfaden für post-humane Computer- und…
32 min
History and implications of DRM
From tractors to Web standards
36 min
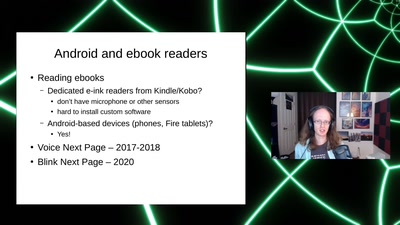
Accessible input for readers, coders, and hackers
From eyelid blinks to speech recognition
60 min
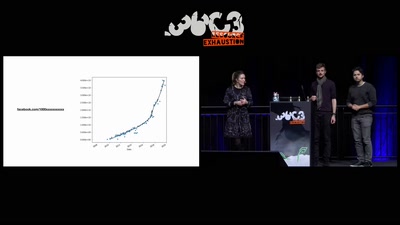
Inside the Fake Like Factories
How thousands of Facebook, You Tube and Instagram pages…

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
55 min
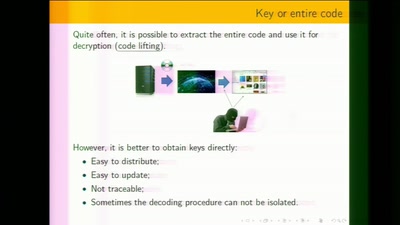
White-Box Cryptography
Survey
35 min
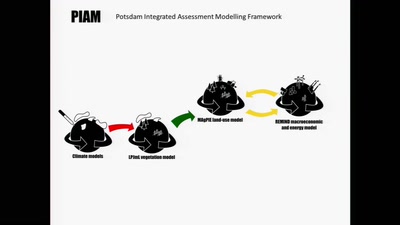
Simulating the future of the global agro-food system
Cybernetic models analyze scenarios of interactions between…
57 min
The Precariat: A Disruptive Class for Disruptive Times.
Why and How the Precariat will define the Global…

40 min
What is this? A machine learning model for ants?
How to shrink deep learning models, and why you would want…
44 min