Search for "ths" returned 9096 results
35 min
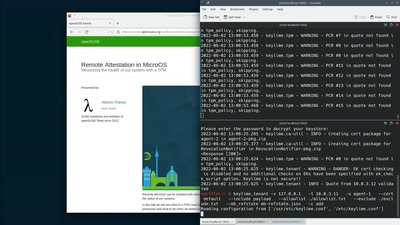
Remote Attestation in MicroOS
Measuring the health of our system with a TPM
41 min
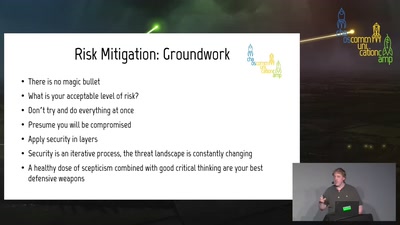
Introduction to (home) network security.
A beginner-friendly guide to network segmentation for…

25 min
Uyuni: introduction, last year's updates and future
What is Uyuni? - What's been going on the last year? -…
60 min
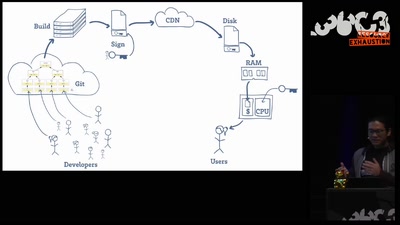
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
30 min
Love, CyBorgs, Art and Open Source – an artistic approach on how to stay golden
How to educate society through the language of art
45 min
Generating uniqueness
How generative art pushes the boundaries of intellectual…
30 min
EOS Design System
The solution to bring good UX to all OSS
58 min
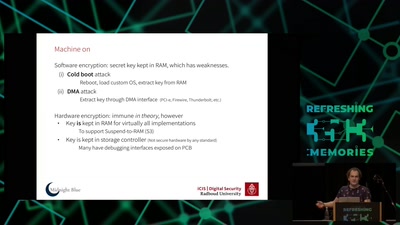
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
65 min
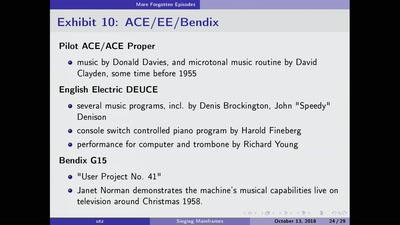
Singing Mainframes
An Unofficial History of the Dawn of Computer Music
38 min
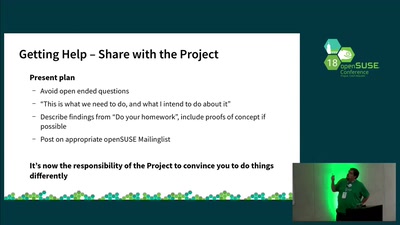
openSUSE is what you make it
How to change anything you want in the project
30 min
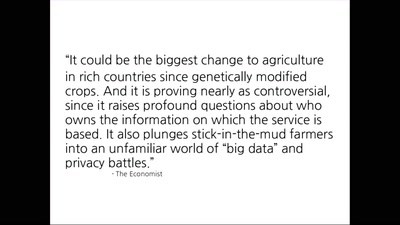
Satellite Imagery in Agriculture
Questioning privacy, data protection, and autonomy in the…
62 min
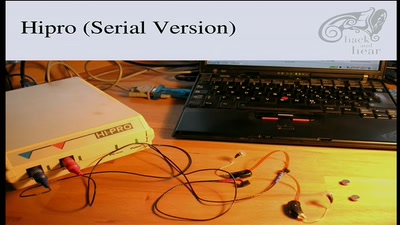
Bionic Ears
Introduction into State-of-the-Art Hearing Aid Technology
65 min
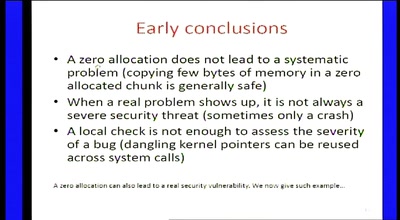
Zero-sized heap allocations vulnerability analysis
Applications of theorem proving for securing the windows…
60 min
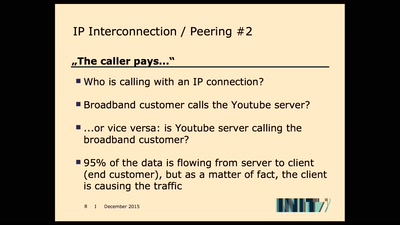
Buffering sucks!
An attempt of calculating the economic cost of buffering.
41 min
Reverse Engineering a pocket synthesizer
from nothing to custom firmware on the OP-1
32 min
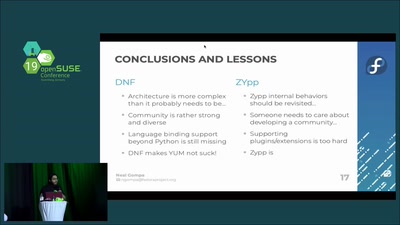
DNF vs ZYpp: Fight!
A comparison of the two major RPM package managers
25 min
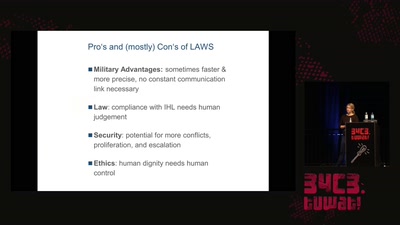
Regulating Autonomous Weapons
The time travelling android isn’t even our biggest problem
33 min
Social cooling
How the reputation economy is turning us into conformists

66 min
Podjournalism
The Role of Podcasting in Critical and Investigative…
82 min
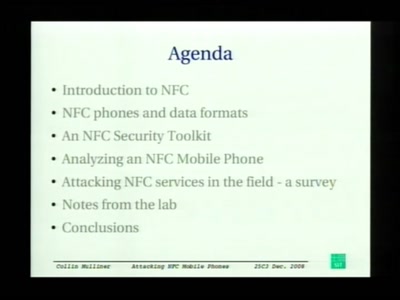
Attacking NFC mobile phones
First look at the security of NFC mobile phones
30 min
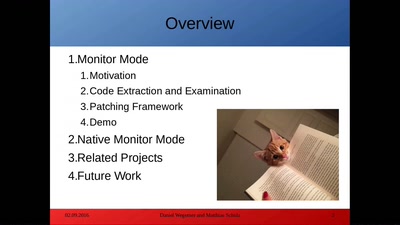
NexMon - Make Wi-Fi hacking on smartphones great again!
Reverse engineering of the Nexus 5 Wi-Fi chip
40 min
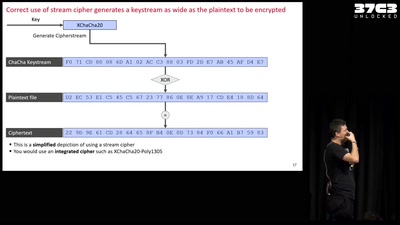
Unlocked! Recovering files taken hostage by ransomware
Decrypting files hijacked by the "second most used…
52 min
No Body's Business But Mine, a dive into Menstruation Apps
The Not-So Secret Data Sharing Practices Of Menstruation…

41 min
Framing digital industry into planetary limits and transition policies
The environmental costs of digital industry and pathways to…
16 min