Search for "ths" returned 9096 results
16 min
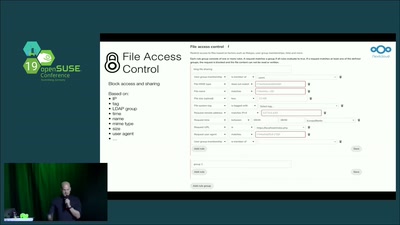
What can you do with a self-hosted alternative to Office365, Google Apps and others
A small selection of the nearly 200 apps for Nextcloud
34 min
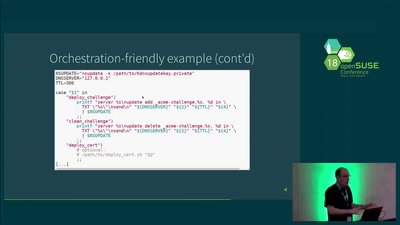
Roadrunner: Securing services with LetsEncrypt
Why you should no longer be afraid of using TLS
33 min
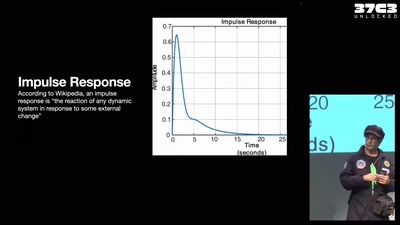
Robot Music
The Robots Play Our Music and What Do We Do?
32 min
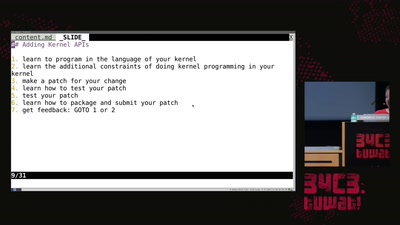
library operating systems
reject the default reality^W abstractions and substitute…
55 min
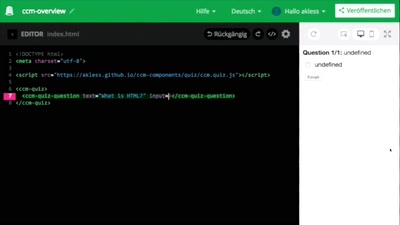
Modular Web
New ways for free software developers to shape the world.
49 min
Does Hacktivism Matter?
How the Btx hack changed computer law-making in Germany
86 min
Certified programming with dependent types
Because the future of defense is liberal application of math
45 min
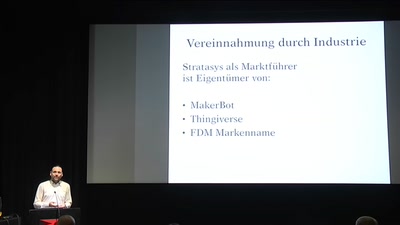
FabLabs are not Hackerspaces!
The story of an art driven 3D printing research facility
31 min
openSUSE ALP prototype on AWS, experimental, but fun!
Experiences, challenges and how SUSE NeuVector came into…
61 min
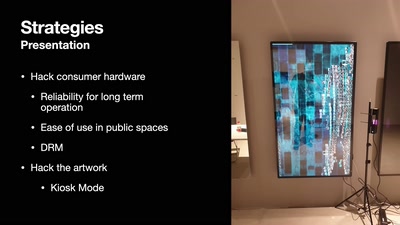
DevOps but for artworks in museums
A look into pipelines ending in museums and not in the cloud
38 min
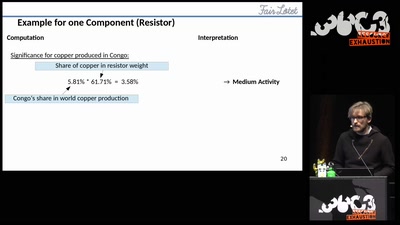
Fairtronics
A Tool for Analyzing the Fairness of Electronic Devices
32 min
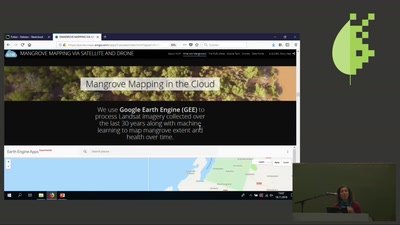
Mangrove Conservation via Satellite
using the latest technology to map and monitor mangroves
37 min
Music on Mars?
A Musical Adventure for Astronauts and the Space Cadets Who…
27 min
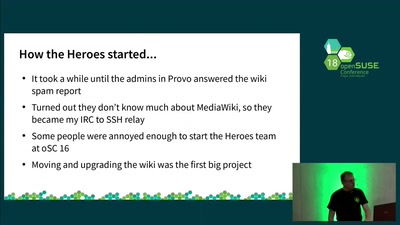
Heroes, not Superheroes
What the Heroes would prefer not to tell you ;-)
44 min
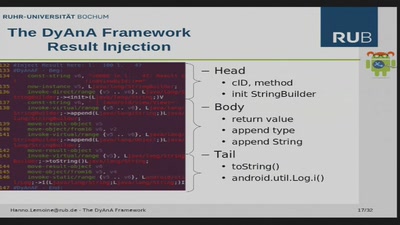
Dynamic Malware Analysis on Android Phones
Presentation of the DyAnA Framework (Dynamic Android…
48 min
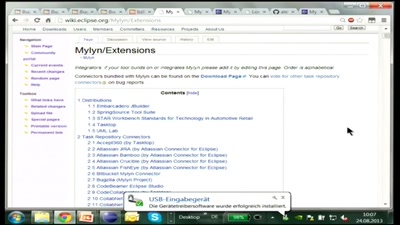
Fokussiertes Arbeiten mit Mylyn
Effectively use the integrated Task-focused UI in Eclipse
63 min
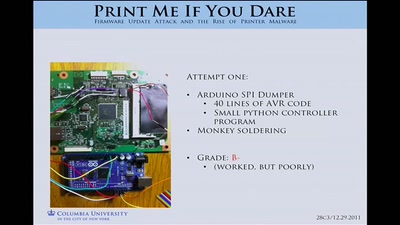
Print Me If You Dare
Firmware Modification Attacks and the Rise of Printer…
38 min
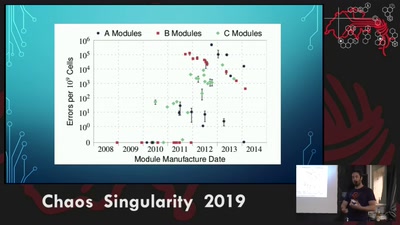
Rowhammer exploit
Viability of the Rowhammer Attack when ECC memory is used
40 min
LibreRouter demo
Lessons learned developing open source hardware for the…
44 min
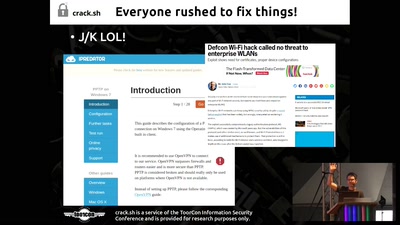
Legacy Crypto Never Dies
Cracking DES nearly 20 years after the EFF DES Cracker
29 min
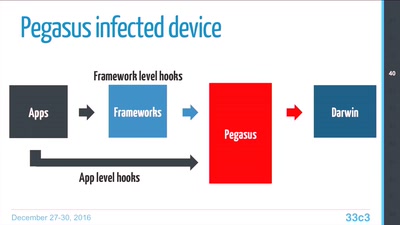
Pegasus internals
Technical Teardown of the Pegasus malware and Trident…

48 min
Oil Into Digits
A short exploration of the relation between energy and…
68 min
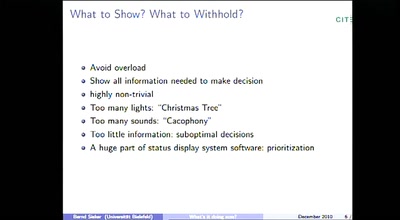
"Spoilers, Reverse Green, DECEL!" or "What's it doing now?"
Thoughts on the Automation and its Human interfaces on…
56 min
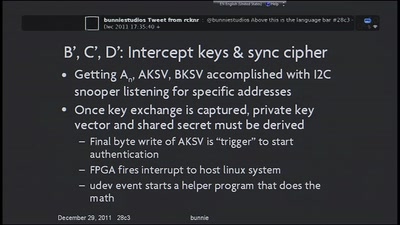
Blackbox JTAG Reverse Engineering
Discovering what the hardware architects try to hide from…
45 min