Search for "Os Keyes" returned 637 results

32 min
Craft, leisure, and end-user innovation
How hacking is conceived in social science research
58 min
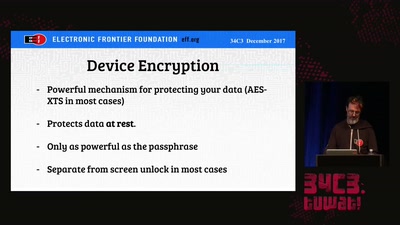
Protecting Your Privacy at the Border
Traveling with Digital Devices in the Golden Age of…

61 min
Ten years after ‚We Lost The War‘
The future does not look much brighter than ten years ago.…
58 min
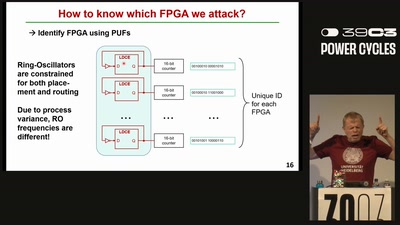
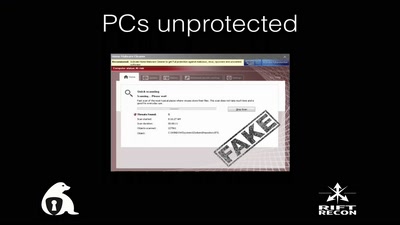
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
60 min
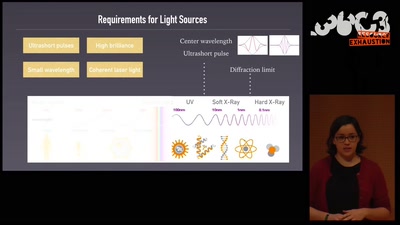
An ultrashort history of ultrafast imaging
Featuring the shortest movies and the largest lasers
49 min
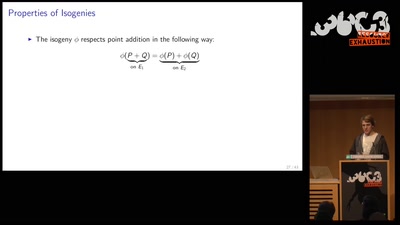
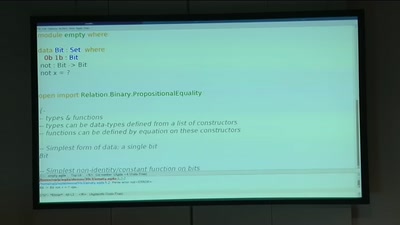
BREACH in Agda
Security notions, proofs and attacks using dependently…
58 min
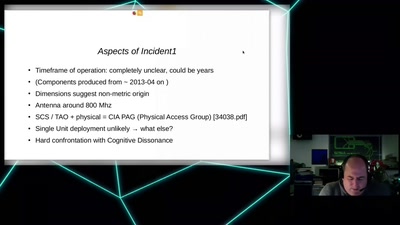
CIA vs. Wikileaks
Intimiditation surveillance and other tactics observed and…

38 min
Afroroutes: Africa Elsewhere
VR experience "Beyond Slavery"
65 min
35C3 Infrastructure Review
Up and to the right: All the statistics about this event…
55 min
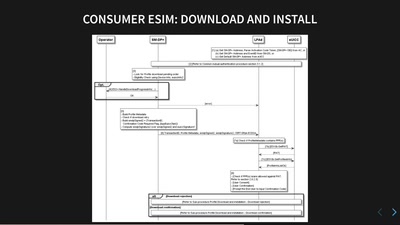
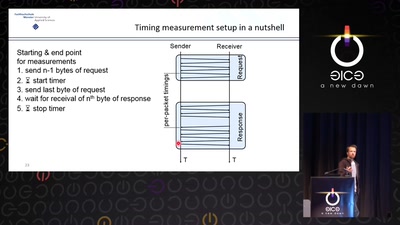
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks

64 min
Cory Doctorow – Fireside Chat
Reading and Q&A

60 min
What does Big Brother see, while he is watching?
Uncovering images from the secret Stasi archives.
44 min
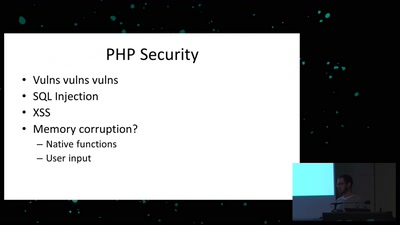
Exploiting PHP7 unserialize
teaching a new dog old tricks
63 min
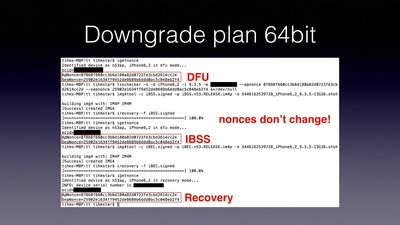
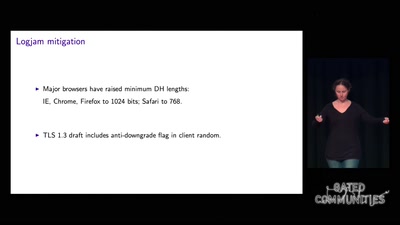
goto fail;
exploring two decades of transport layer insecurity
47 min