Search for "B@lu" returned 3436 results

51 min
How to contribute to make open hardware happen
Mooltipass, Openpandora/Pyra and Novena/Senoko: how I…
60 min
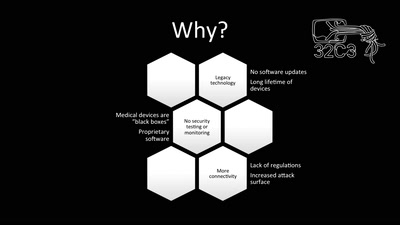
Unpatchable
Living with a vulnerable implanted device
58 min
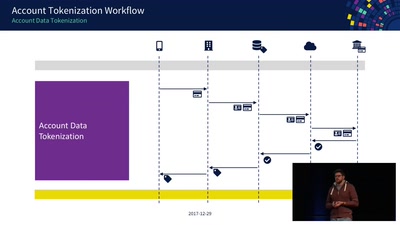
Decoding Contactless (Card) Payments
An Exploration of NFC Transactions and Explanation How…

62 min
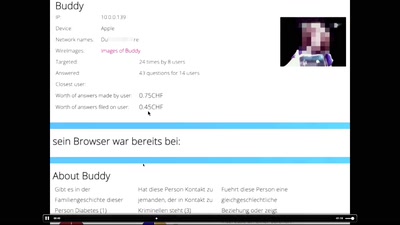
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…

58 min
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
54 min
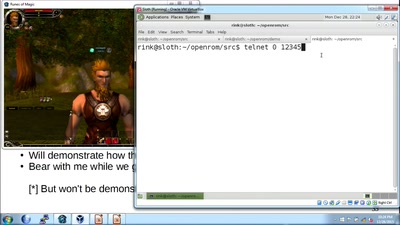
How hackers grind an MMORPG: by taking it apart!
An introduction to reverse engineering network protocols

59 min
Security of the IC Backside
The future of IC analysis
59 min
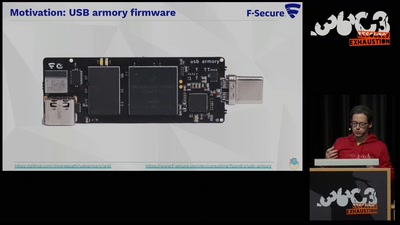
TamaGo - bare metal Go framework for ARM SoCs.
Reducing the attack surface with pure embedded Go.

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
62 min
Calafou, postcapitalist ecoindustrial community
Building a space for grassroots sustainable technology…
60 min
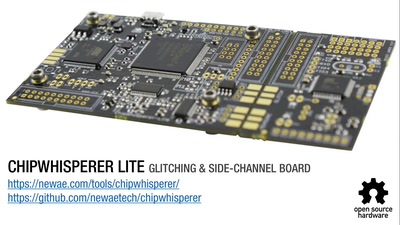
Opening Closed Systems with GlitchKit
'Liberating' Firmware from Closed Devices with Open Source…
62 min
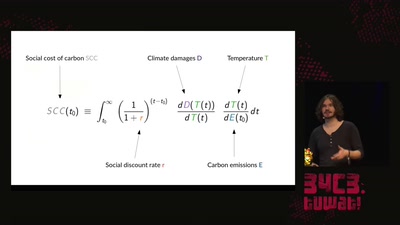
A hacker's guide to Climate Change - What do we know and how do we know it?
An introduction to the basics of climate research and what…
62 min
The Ghost in the Machine
An Artificial Intelligence Perspective on the Soul
61 min
The architecture of a street level panopticon
How drones, IMSI Catchers, and cameras are shaping our…
58 min