Search for "Lea Rain" returned 1165 results

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
30 min
On Computing Numbers, with an Application to Problems of our Society
Journalism ♥ Computer Science
69 min
cryptocurrencies, smart contracts, etc.: revolutionary tech?
short answer: Yes!
61 min
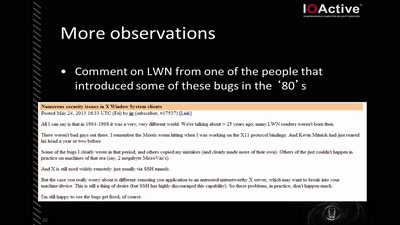
X Security
It's worse than it looks
55 min
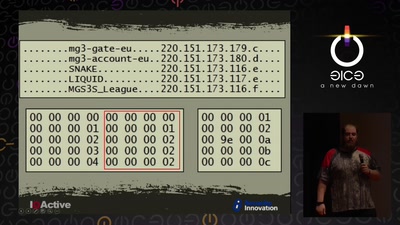
Cyber Necromancy
Reverse Engineering Dead Protocols
60 min
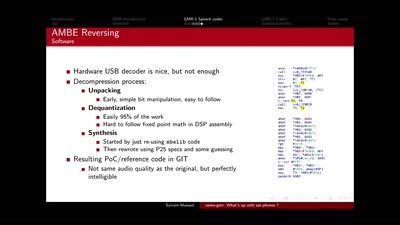
osmo-gmr: What's up with sat-phones ?
Piecing together the missing bits
43 min
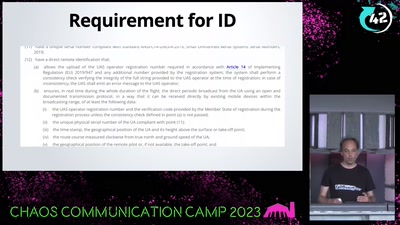
WTF DJI, UAV CTF?!
A hacker's view at commercial drone security
58 min
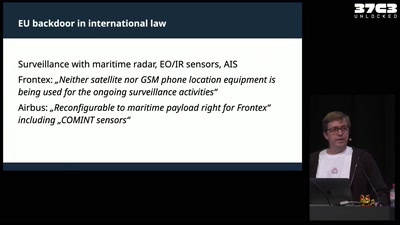
A Libyan Militia and the EU - A Love Story?
Open-Source investigating Tareq Ben Zeyad Brigade and their…
61 min
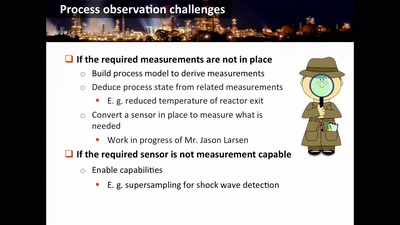
Damn Vulnerable Chemical Process
Exploitation in a new media
62 min
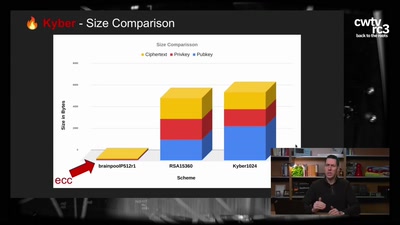
Kyber and Post-Quantum Crypto
How does it work?
31 min
The woman behind your WiFi
Hedy Lamarr: Frequency Hopping in Hollywood
29 min
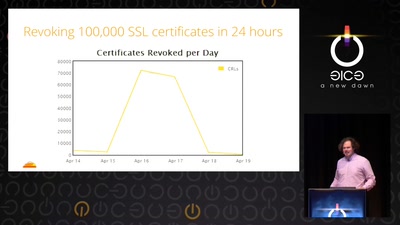
Heartache and Heartbleed: The insider’s perspective on the aftermath of Heartbleed
The untold story of what really happened, how it was…

61 min