Search for "Os Keyes" returned 637 results
42 min
Reverse engineering FPGAs
Dissecting FPGAs from bottom up, extracting schematics and…

60 min
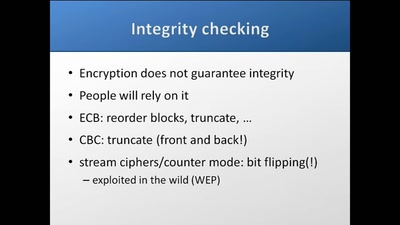
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
55 min
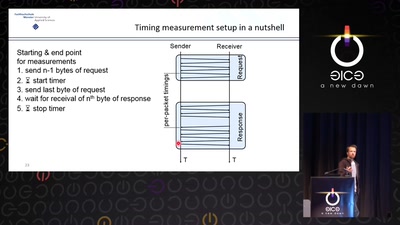
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks
61 min
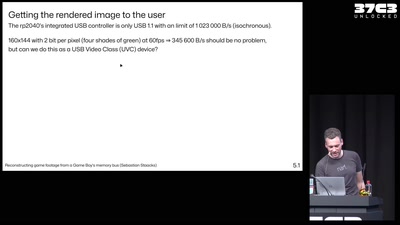
Reconstructing game footage from a Game Boy's memory bus
The GB Interceptor

60 min
What does Big Brother see, while he is watching?
Uncovering images from the secret Stasi archives.
65 min
35C3 Infrastructure Review
Up and to the right: All the statistics about this event…
62 min
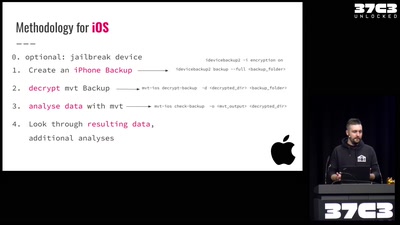
Einführung in Smartphone Malware Forensik
Wie man Stalkerware und Staatstrojaner auf Smartphones…

32 min
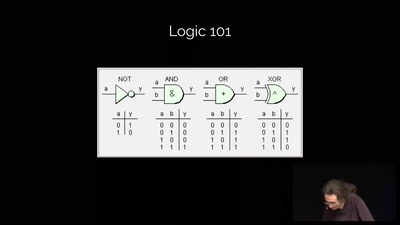
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
53 min
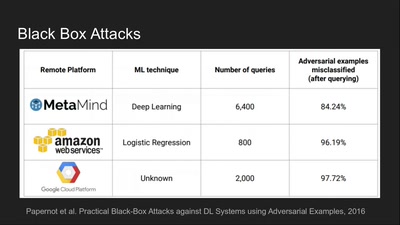
Deep Learning Blindspots
Tools for Fooling the "Black Box"

60 min
Quantum Cryptography
from key distribution to position-based cryptography
39 min
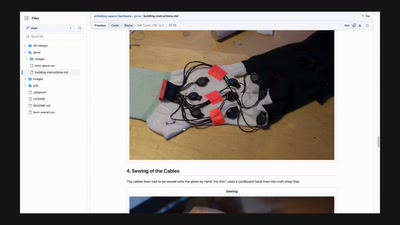
The Unfolding Space Glove
A Wearable for the Visually Impaired Translating 3D Vision…
64 min