Search for "ICAN" returned 3962 results
57 min
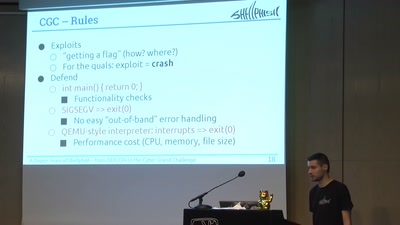
A Dozen Years of Shellphish
From DEFCON to the DARPA Cyber Grand Challenge

31 min
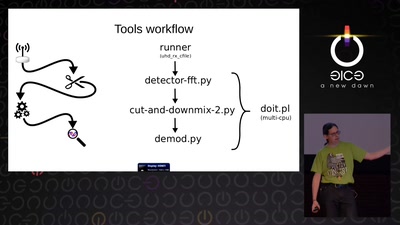
Demystifying Network Cards
Things you always wanted to know about NIC drivers
61 min
Code Pointer Integrity
... or how we battle the daemons of memory safety
38 min
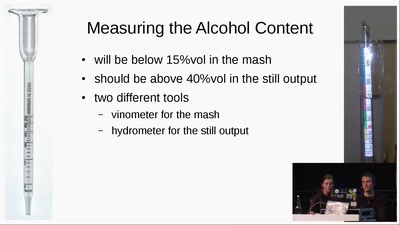
Schnaps Hacking
from apple to schnaps -- a complete diy-toolchain
34 min
Ling - High level system programming
modular and precise resource management
62 min
radare demystified
after 1.0
55 min
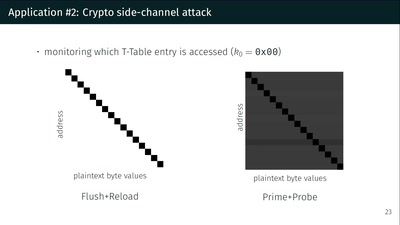
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
61 min
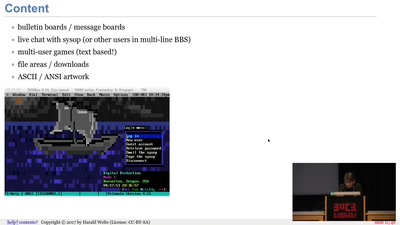
BBSs and early Internet access in the 1990ies
Modems, FIDO, Z-Netz, Usenet, UUCP, SLIP and ISDN
60 min
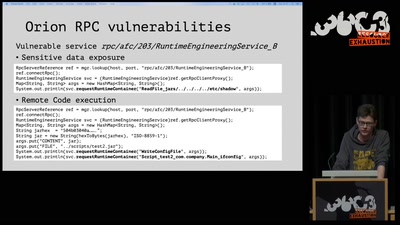
On the insecure nature of turbine control systems in power generation
A security study of turbine control systems in power…
60 min
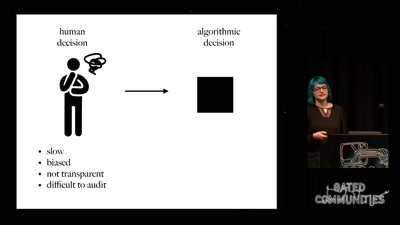
Prediction and Control
Watching Algorithms

77 min