Search for "Theo Voss" returned 438 results

41 min
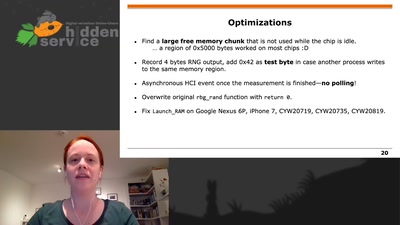
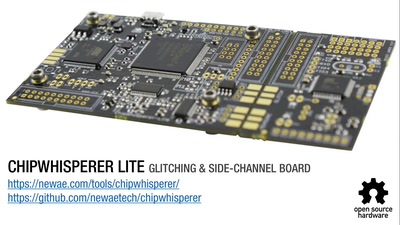
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
49 min
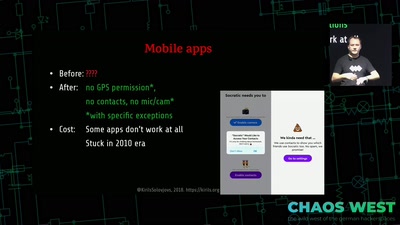
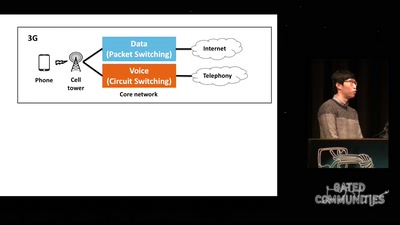
Dissecting VoLTE
Exploiting Free Data Channels and Security Problems

32 min
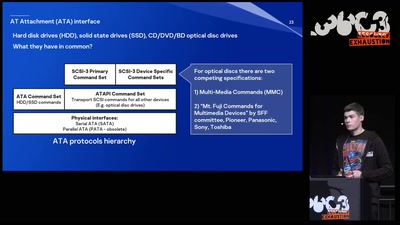
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
60 min
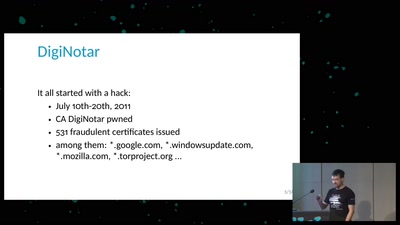
Everything you always wanted to know about Certificate Transparency
(but were afraid to ask)
64 min
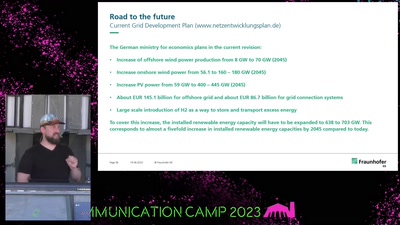
We only have one earth
A case for expansionistic space policy
30 min
All Our Shared Spectrum Are Belong to Us
Visualizing WLAN Channel Usage on OpenWRT
60 min
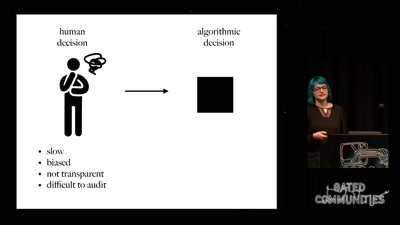
Prediction and Control
Watching Algorithms
59 min
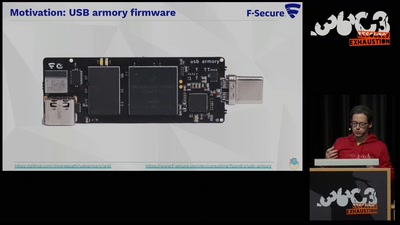
TamaGo - bare metal Go framework for ARM SoCs.
Reducing the attack surface with pure embedded Go.
46 min
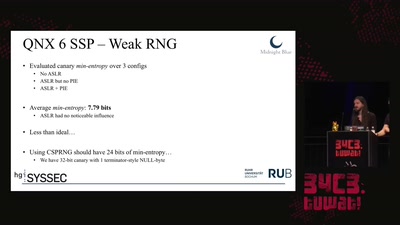
Taking a scalpel to QNX
Analyzing & Breaking Exploit Mitigations and Secure Random…
44 min
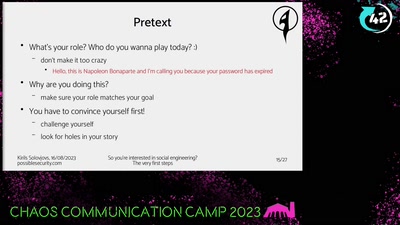
So you're interested in social engineering?
The very first steps
60 min
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
58 min
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
59 min
Visiting The Bear Den
A Journey in the Land of (Cyber-)Espionage
60 min