Search for "sECuRE" returned 800 results
55 min
ZombieLoad Attack
Leaking Your Recent Memory Operations on Intel CPUs

42 min
Citzens or subjects? The battle to control our bodies, speech and communications
A call to action to defend our ePrivacy and eliminate…
41 min
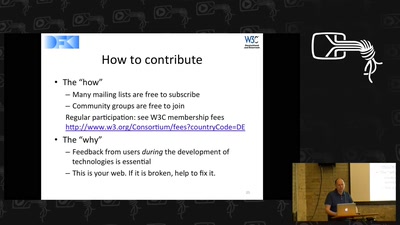
NGI Zero: A treasure trove of IT innovation
Resilient. Trustworthy. Sustainably Open.

60 min
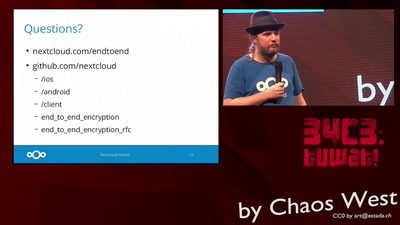
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
49 min
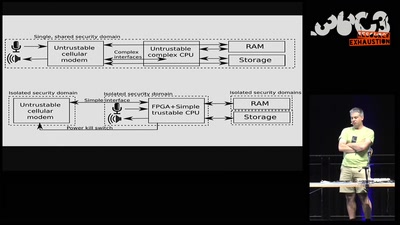
Creating Resilient and Sustainable Mobile Phones
Be prepared for the coming Digital Winter. And play…
10 min
Premiere: We love surveillance
#7reasons
46 min
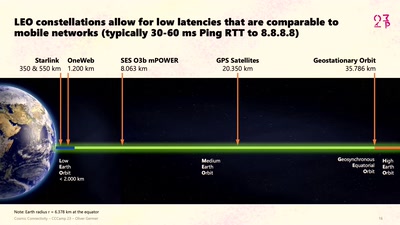
Cosmic Connectivity
Starlink, Satellite Swarms, and the Hackers' Final Frontier

41 min
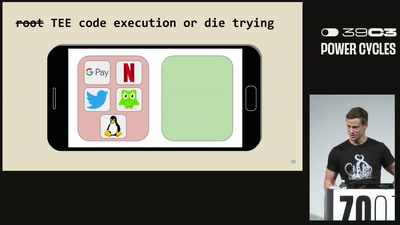
Build a Fake Phone, Find Real Bugs
Qualcomm GPU Emulation and Fuzzing with LibAFL QEMU
39 min
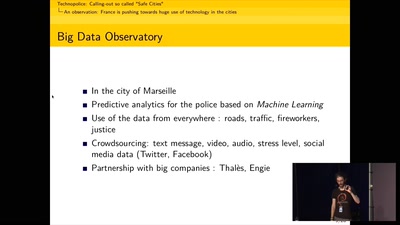
Technopolice: calling out so-called "Safe Cities"
Decentralising the fight against automated surveillance in…
45 min
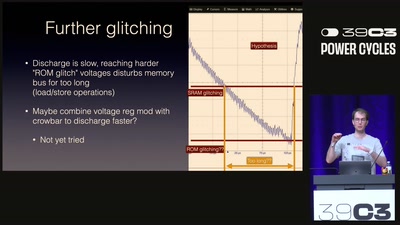
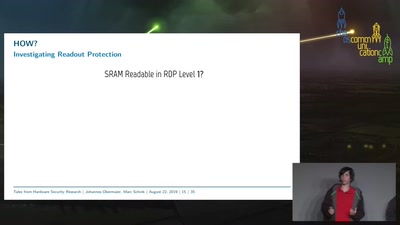
Tales from Hardware Security Research
From Research over Vulnerability Discovery to Public…
32 min
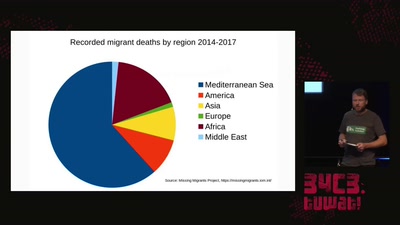
The seizure of the Iuventa
How search and rescue in the mediterranean was criminalized
56 min
Planes and Ships and Saving Lives
How soft and hardware can play a key role in saving lives…
34 min