Search for "Max" returned 4697 results
60 min
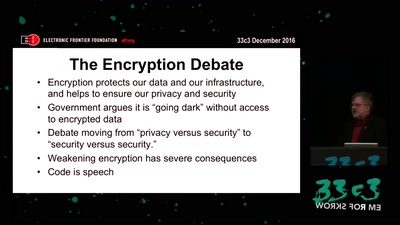
The Fight for Encryption in 2016
Crypto fight in the Wake of Apple v. FBI

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities

61 min
The Invisible Committee Returns with "Fuck Off Google"
Cybernetics, Anti-Terrorism, and the ongoing case against…
53 min
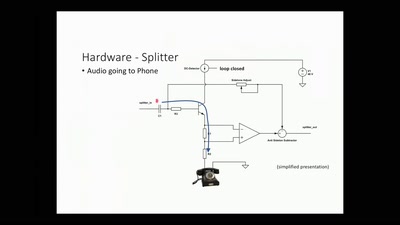
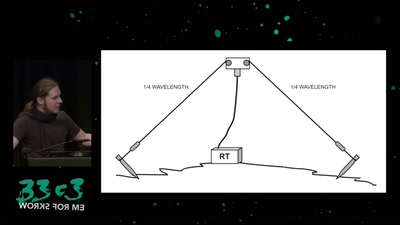
Surveilling the surveillers
About military RF communication surveillance and other…
32 min
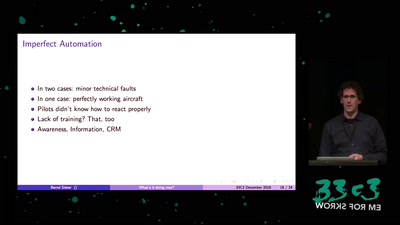
What's It Doing Now?
The Role of Automation Dependency in Aviation Accidents

59 min
Develop Secure Software - The DevGuard Project
OSS Security von Entwicklern für Entwickler

41 min
Framing digital industry into planetary limits and transition policies
The environmental costs of digital industry and pathways to…
46 min
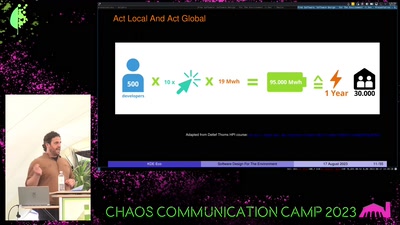
Free Software
Software Design For The Environment
32 min
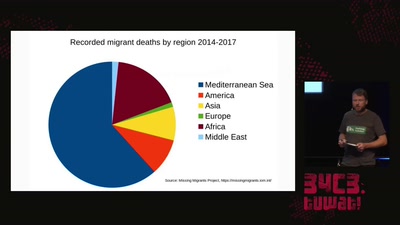
The seizure of the Iuventa
How search and rescue in the mediterranean was criminalized

66 min
The Snowden Refugees under Surveillance in Hong Kong
A Rapidly Emerging Police State and Imminent Deportation to…

55 min