Search for "Nick Farr" returned 847 results

57 min
Everything you want to know about x86 microcode, but might have been afraid to ask
An introduction into reverse-engineering x86 microcode and…

61 min
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…
60 min
The Perl Jam 2
The Camel Strikes Back
38 min
ARMore: Pushing Love Back Into Binaries
Aarch64 binary rewriting adventures but mostly pains
60 min
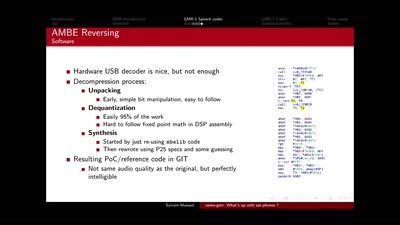
osmo-gmr: What's up with sat-phones ?
Piecing together the missing bits

59 min
Hacking EU funding for a decentralizing FOSS project
Understanding and adapting EU legal guidelines from a FOSS…
58 min
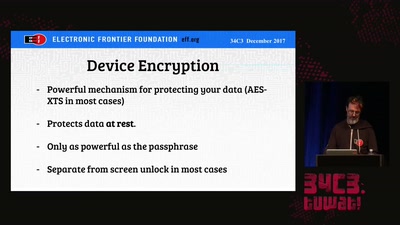
Protecting Your Privacy at the Border
Traveling with Digital Devices in the Golden Age of…
35 min
Ethics in the data society
Power and politics in the development of the driverless car
47 min
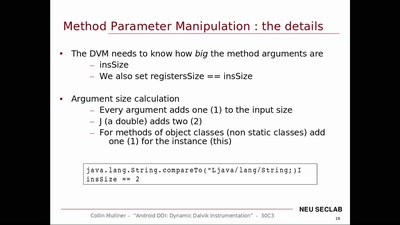
Android DDI
Dynamic Dalvik Instrumentation of Android Applications and…
35 min
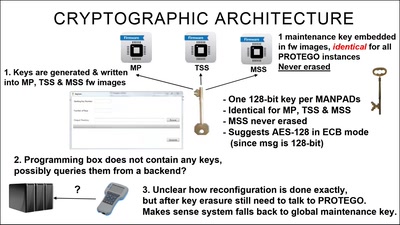
Harry Potter and the Not-So-Smart Proxy War
Taking a look at a covert CIA virtual fencing solution
60 min
Lifting the Fog on Red Star OS
A deep dive into the surveillance features of North Korea's…
46 min
Climate Modelling
The Science Behind Climate Reports
51 min
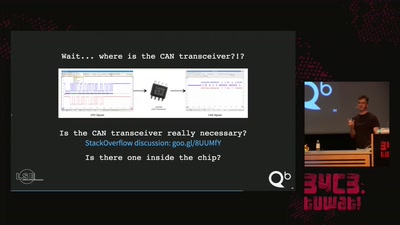
How to drift with any car
(without your mom yelling at you)

53 min
No Love for the US Gov.
Why Lauri Love’s case is even more important than you…
61 min
Code Pointer Integrity
... or how we battle the daemons of memory safety

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
61 min
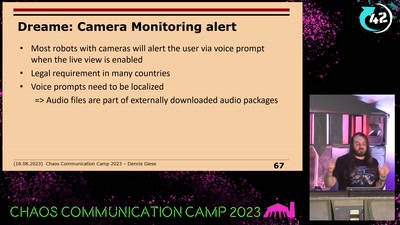
Vacuum robot security and privacy
prevent your robot from sucking your data

60 min