Search for "Nina" returned 474 results

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
61 min
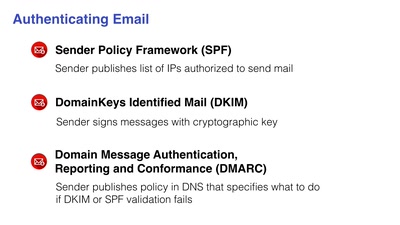
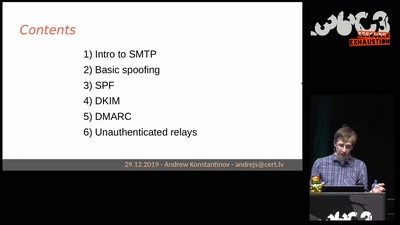
Email authentication for penetration testers
When SPF is not enough

60 min
HAL - The Open-Source Hardware Analyzer
A dive into the foundations of hardware reverse engineering…

68 min
#afdwegbassen: Protest, (Club-)Kultur und antifaschistischer Widerstand
Über kreative Organisation, poltische Aktionen und das…
51 min
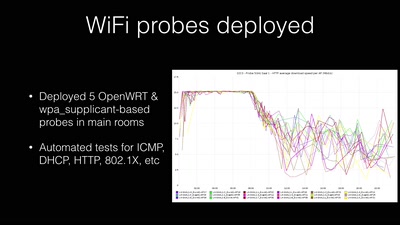
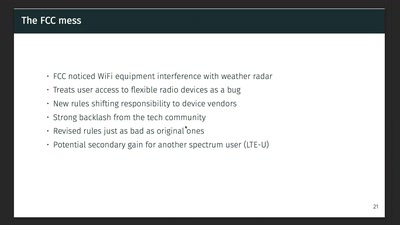
Wireless Drivers: Freedom considered harmful?
An OpenWrt perspective on the development of Linux 802.11…
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
55 min
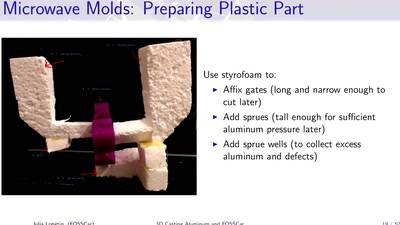
3D Casting Aluminum
Too Much Fun with Microwaves
60 min
Sneaking In Network Security
Enforcing strong network segmentation, without anyone…
58 min
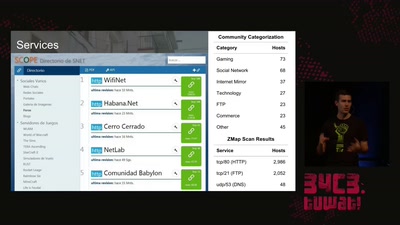
The Internet in Cuba: A Story of Community Resilience
Get a unique tour of some of the world’s most unusual…
61 min
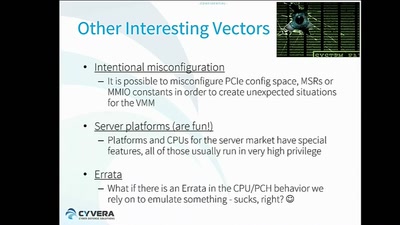
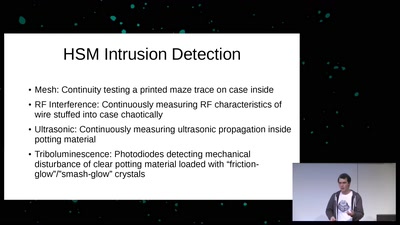
Untrusting the CPU
A proposal for secure computing in an age where we cannot…
53 min
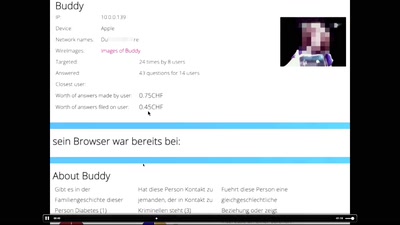
When algorithms fail in our personal lives
Social media break up coordinator

69 min
Telescope Making
How to make your own telescope
54 min
10 Jahre OpenStreetMap
Wir leben noch und zwar sehr gut.

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database

62 min
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…

58 min