Search for "Eva" returned 531 results
71 min
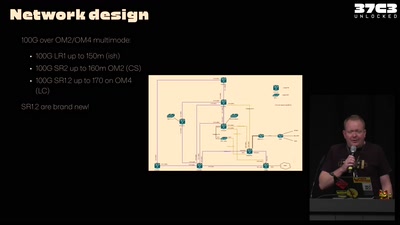
37C3 Infrastructure Review
Teams presenting how they helped making this awesome event
55 min
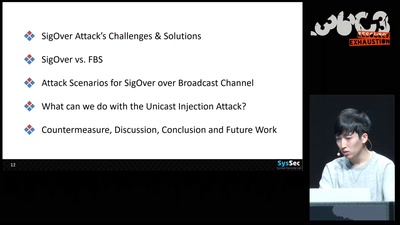
SigOver + alpha
Signal overshadowing attack on LTE and its applications
58 min
How risky is the software you use?
CITL: Quantitative, Comparable Software Risk Reporting
67 min
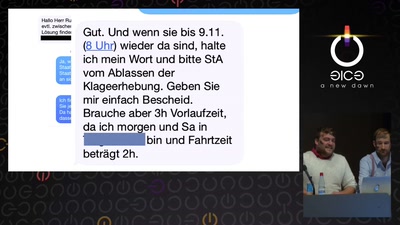
Mit Kunst die Gesellschaft hacken
Das Zentrum für politische Schönheit
60 min
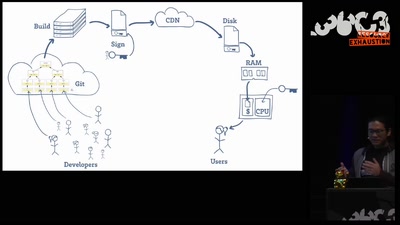
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
59 min
Visiting The Bear Den
A Journey in the Land of (Cyber-)Espionage

95 min
The Time is Right
Ein Science-Fiction-Theaterstück
55 min
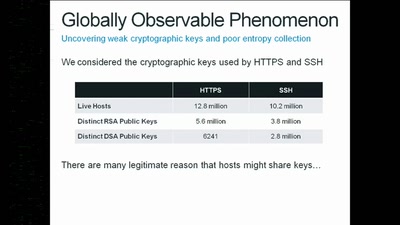
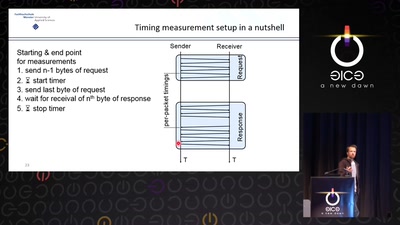
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks
51 min
The GNU Name System
A Decentralized PKI For Social Movements
63 min
Das nützlich-unbedenklich Spektrum
Können wir Software bauen, die nützlich /und/ unbedenklich…
64 min
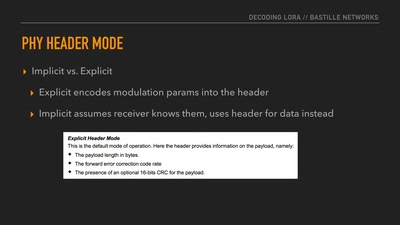
Decoding the LoRa PHY
Dissecting a Modern Wireless Network for the Internet of…
46 min
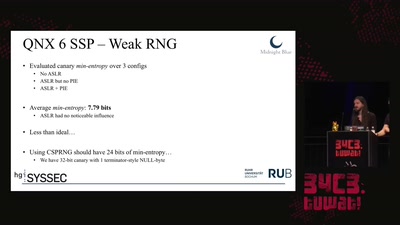
Taking a scalpel to QNX
Analyzing & Breaking Exploit Mitigations and Secure Random…

56 min
Household, Totalitarianism and Cyberspace
Philosophical Perspectives on Privacy Drawing on the…
60 min
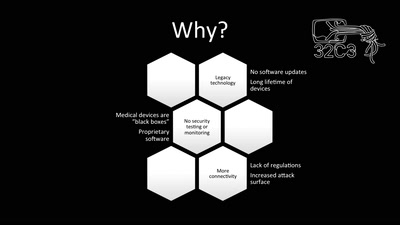
Unpatchable
Living with a vulnerable implanted device
50 min
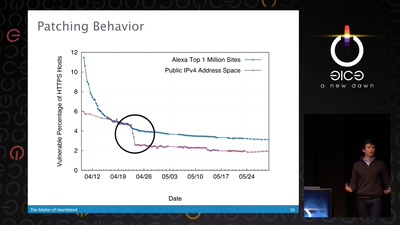
The Matter of Heartbleed
What went wrong, how the Internet reacted, what we can…

58 min