Search for "Seth Hardy" returned 901 results
32 min
library operating systems
reject the default reality^W abstractions and substitute…
38 min
ARMore: Pushing Love Back Into Binaries
Aarch64 binary rewriting adventures but mostly pains
31 min
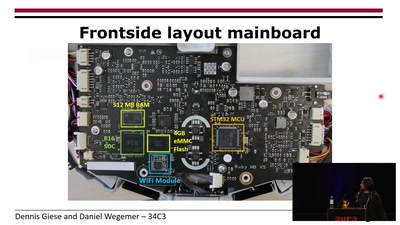
Unleash your smart-home devices: Vacuum Cleaning Robot Hacking
Why is my vacuum as powerful as my smartphone?
63 min
Analyze the Facebook algorithm and reclaim data sovereignty
Algorithms define your priorities. Who else besides you can…
58 min
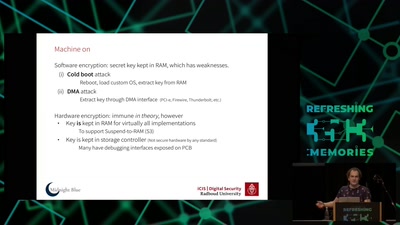
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
42 min
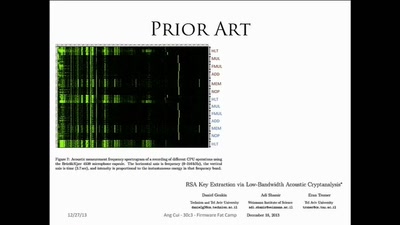
Firmware Fat Camp
Embedded Security Using Binary Autotomy
56 min
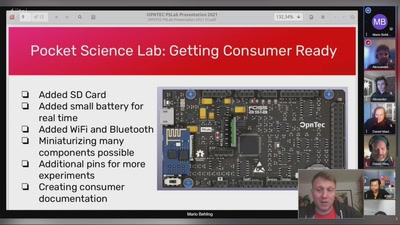
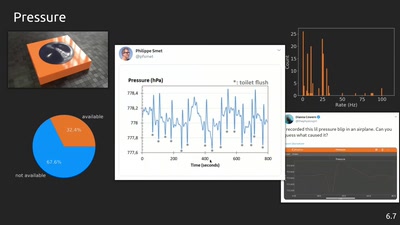
phyphox: Using smartphone sensors for physics experiments
An open source project for education, research and tinkering
40 min
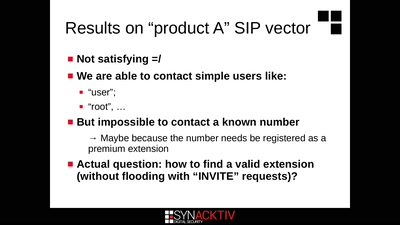
Intercoms Hacking
Call the frontdoor to install your backdoors
59 min
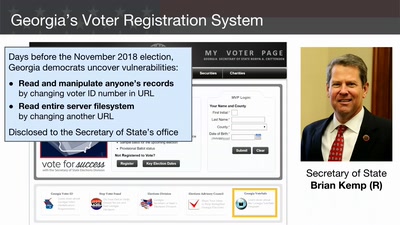
Election Cybersecurity Progress Report
Will the U.S. be ready for 2020?
59 min
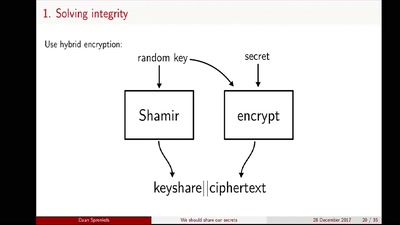
We should share our secrets
Shamir secret sharing: How it works and how to implement it
32 min
Visceral Systems
Approaches to working with sound and network data…
55 min
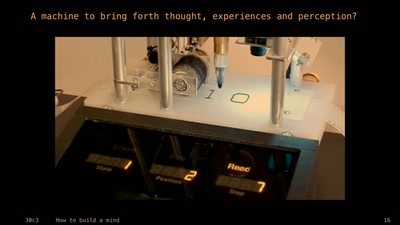
How to Build a Mind
Artificial Intelligence Reloaded

62 min