Search for "Jim" returned 5091 results
62 min
The Internet (Doesn't) Need Another Security Guide
Creating Internet Privacy and Security Resources That Don't…
21 min
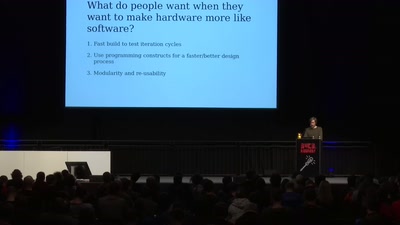
Designing PCBs with code
Is designing circuits with code instead of CAD the future…
33 min
institutions for Resolution Disputes
Rosa Menkman investigates video compression, feedback, and…
38 min
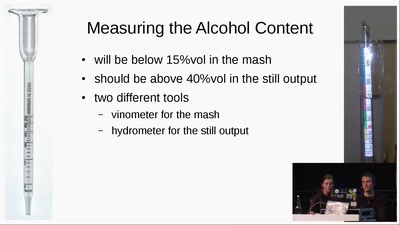
Schnaps Hacking
from apple to schnaps -- a complete diy-toolchain

29 min
Perfect Paul
On Freedom of Facial Expression

25 min
»Hard Drive Punch«
Destroying data as a performative act

38 min
Afroroutes: Africa Elsewhere
VR experience "Beyond Slavery"
26 min
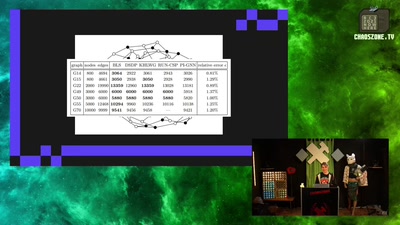
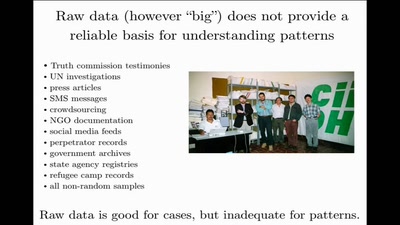
Data Mining for Good
Using random sampling, entity resolution, communications…
37 min
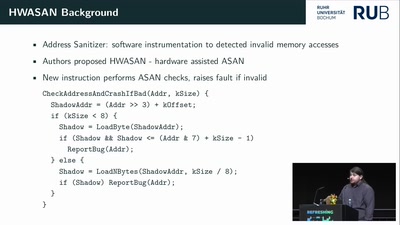
Inside the AMD Microcode ROM
(Ab)Using AMD Microcode for fun and security

43 min
Speaking Fiction To Power
Strategies and tactics to ‘hack’ public spaces and social…
36 min
A Blockchain Picture Book
Blockchain origins and related buzzwords, described in…
35 min
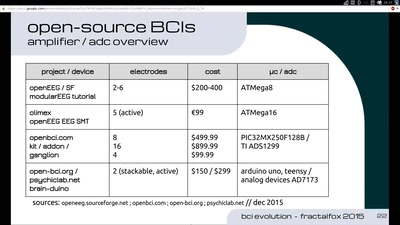
Evolution of Brain-Computer Interfaces
The future of Neuro-Headsets and concepts towards…
60 min
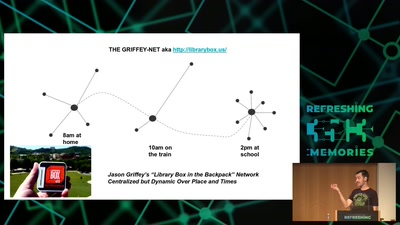
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities

59 min
Hacking EU funding for a decentralizing FOSS project
Understanding and adapting EU legal guidelines from a FOSS…
60 min