Search for "ar3itrary" returned 269 results
62 min
Post Memory Corruption Memory Analysis
Automating exploitation of invalid memory writes
30 min
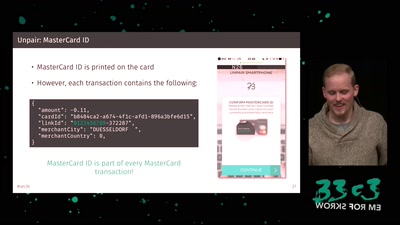
Shut Up and Take My Money!
The Red Pill of N26 Security
58 min
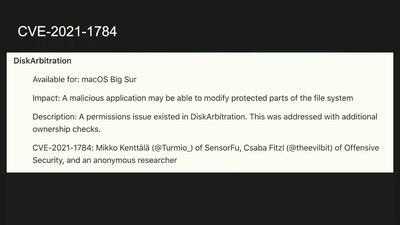
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
42 min
Wifibroadcast
How to convert standard wifi dongles into digital broadcast…
50 min
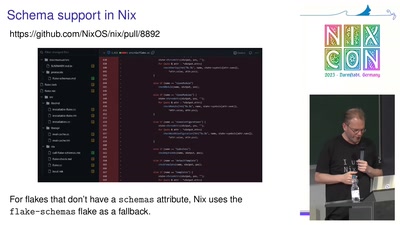
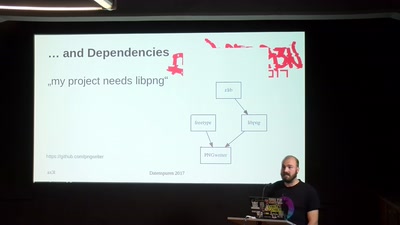
Modern Software Packaging for Developers
Wait, how to install your FOSS project again?
48 min
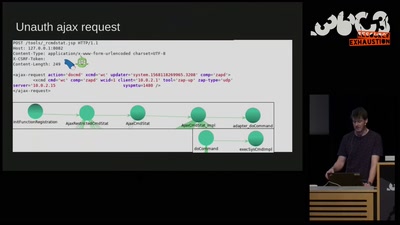
Don't Ruck Us Too Hard - Owning Ruckus AP Devices
3 different RCE vulnerabilities on Ruckus Wireless access…
63 min
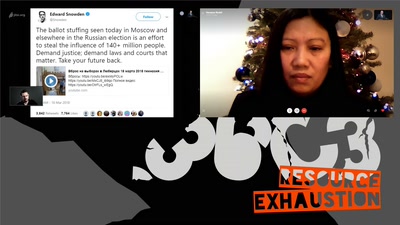
Human Rights at a Global Crossroads
Whistleblowers and the Cases of The Snowden Refugees and…
41 min