Search for "t" returned 10539 results
53 min
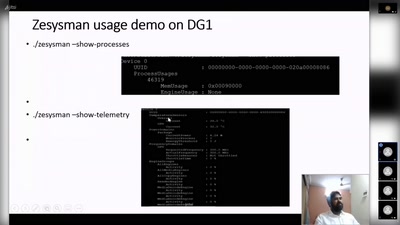
TBM: Trusted boot module
NLNet sponsored (open hardware) trusted boot module

49 min
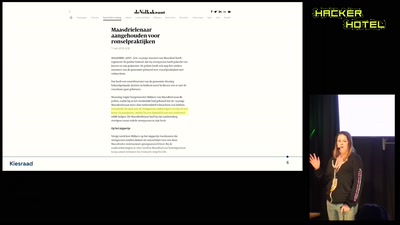
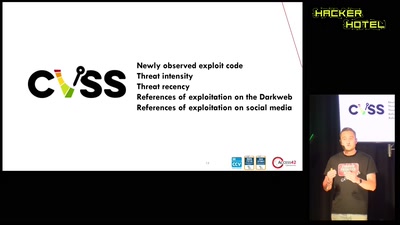
Scanning and reporting vulnerabilities for the whole IPv4 space.
How the Dutch Institute for Vulnerability Disclosure scales…
43 min
Van Gogh TV - Piazza virtuale
Hallo hallo ist da jemand?

35 min
Don't Fear the Reboot
Embracing an Immutable-Friendly Mindset

46 min
The Mission of the MV Louise Michel
"Feminism will be anti-racist or it won´t be"
55 min
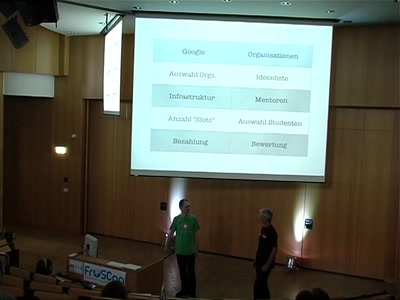
Google Summer of Code
Neue Mitstreiter mit Geld (und T-Shirts) gewinnen - klappt…
17 min