Search for "wonko" returned 40 results

46 min
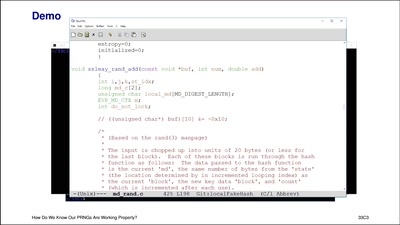
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
61 min
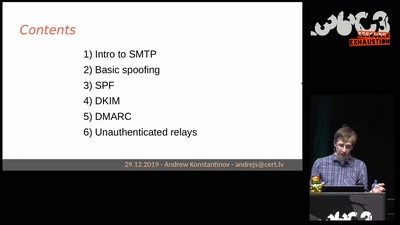
Email authentication for penetration testers
When SPF is not enough

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
36 min
A Blockchain Picture Book
Blockchain origins and related buzzwords, described in…
64 min
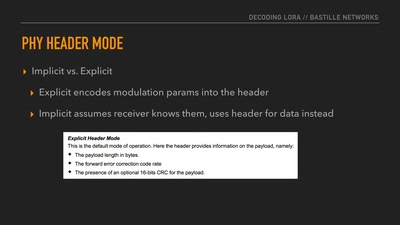
Decoding the LoRa PHY
Dissecting a Modern Wireless Network for the Internet of…
63 min
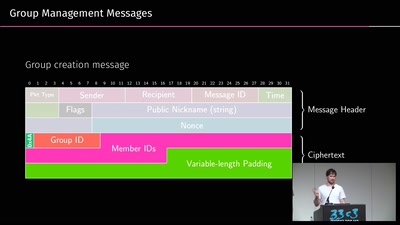
A look into the Mobile Messaging Black Box
A gentle introduction to mobile messaging and subsequent…

37 min