Search for "W. Heck" returned 1261 results
63 min
Human Rights at a Global Crossroads
Whistleblowers and the Cases of The Snowden Refugees and…

58 min
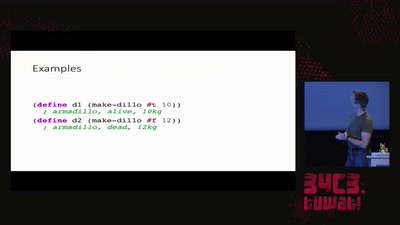
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
43 min
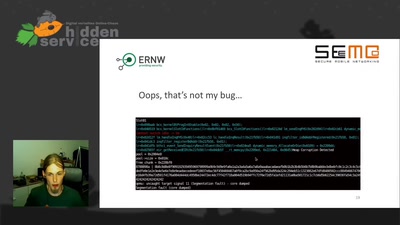
No PoC? No Fix! - A sad Story about Bluetooth Security
It is just a broken memcpy in the Bluetooth stack. Do we…
33 min
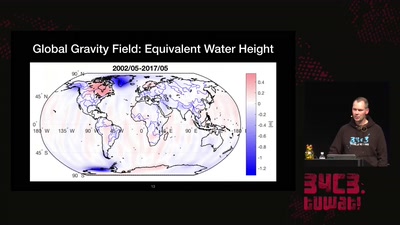
Watching the changing Earth
warning: gravity ahead
62 min
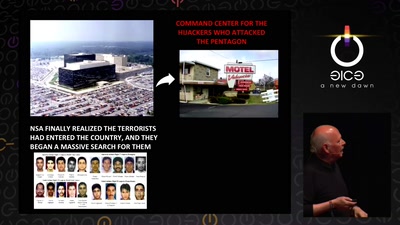
Tell no-one
A century of secret deals between the NSA and the telecom…
31 min
Growing Up Software Development
From Hacker Culture to the Software of the Future
47 min
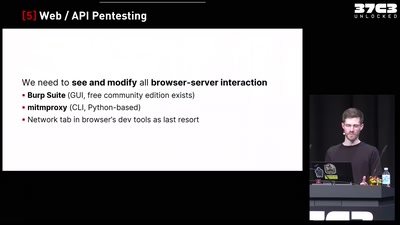
Finding Vulnerabilities in Internet-Connected Devices
A Beginner’s Guide
60 min
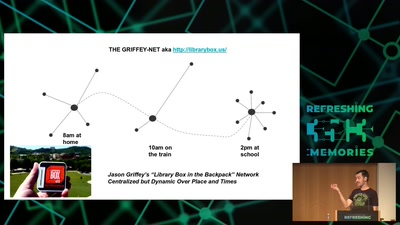
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
59 min
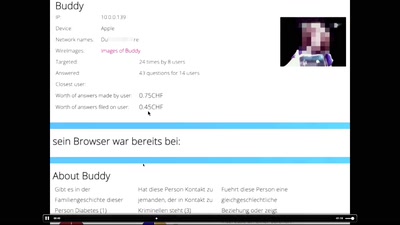
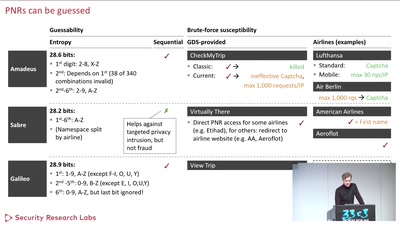
Where in the World Is Carmen Sandiego?
Becoming a secret travel agent

61 min
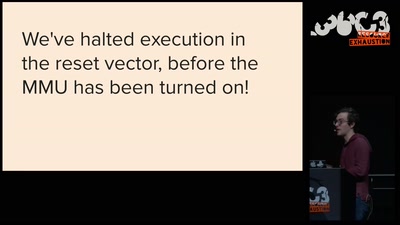
wallet.fail
Hacking the most popular cryptocurrency hardware wallets
60 min
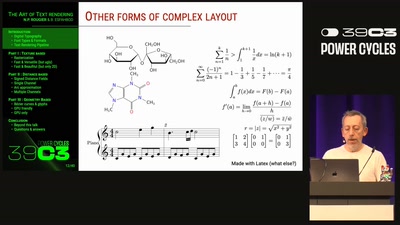
Why is GPG "damn near unusable"?
An overview of usable security research
60 min
APT Reports and OPSEC Evolution, or: These are not the APT reports you are looking for
How advanced threat actors learn and change with innovation…
57 min
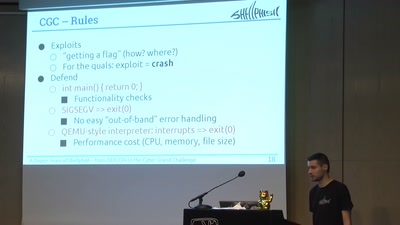
A Dozen Years of Shellphish
From DEFCON to the DARPA Cyber Grand Challenge
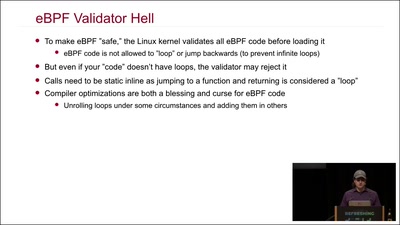
54 min