Search for "Jim" returned 5093 results
51 min
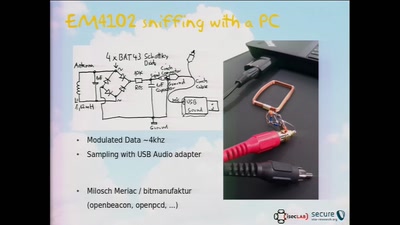
Open Source in the WSN Research
Experiences made with free and open source software in…
58 min
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
60 min
On the insecure nature of turbine control systems in power generation
A security study of turbine control systems in power…

60 min
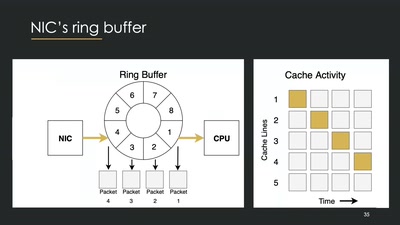
Building a high throughput low-latency PCIe based SDR
Lessons learnt implementing PCIe on FPGA for XTRX Software…
32 min
Technology and Mass Atrocity Prevention
Overview on Current Efforts - We Need Moar H4x0rs?!

87 min
OPENCOIL – A Roaming Speedshow
or the fine art of appropriating inductive charging pads in…
52 min
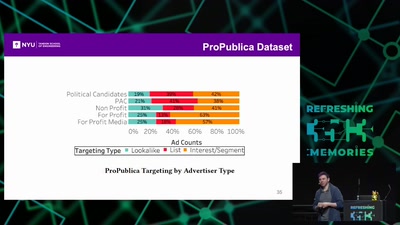
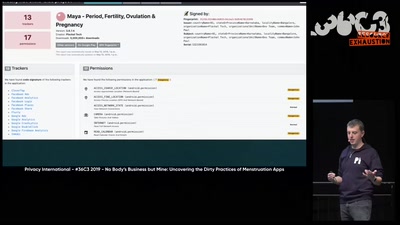
No Body's Business But Mine, a dive into Menstruation Apps
The Not-So Secret Data Sharing Practices Of Menstruation…

33 min
Interplanetary Colonization
the state at the beginning of the 21st Century
35 min
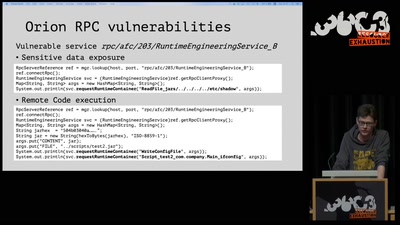
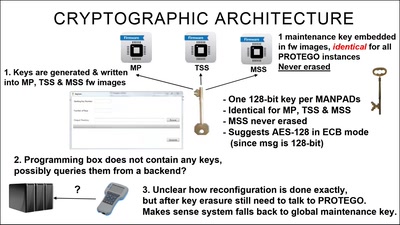
Harry Potter and the Not-So-Smart Proxy War
Taking a look at a covert CIA virtual fencing solution

38 min
Content take-downs: Who cleans the internet?
EU plans to swipe our freedom of expression under the carpet
60 min
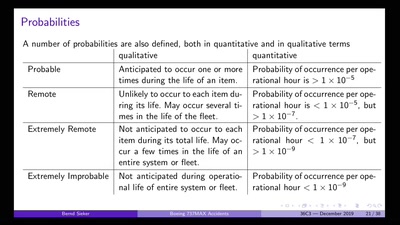
Boeing 737MAX: Automated Crashes
Underestimating the dangers of designing a protection system
42 min
Wifibroadcast
How to convert standard wifi dongles into digital broadcast…

37 min
The foodsaving grassroots movement
How cooperative online structures can facilitate…
55 min
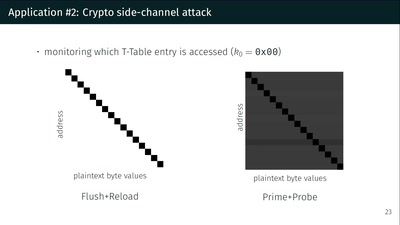
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…
39 min
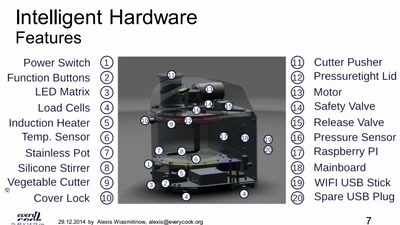
Why do we need an open food information platform
We want all data about food to be linked and public

43 min
This is NOT a proposal about mass surveillance!
Analysing the terminology of the UK’s Snooper’s Charter
64 min
On the Security and Privacy of Modern Single Sign-On in the Web
(Not Only) Attacks on OAuth and OpenID Connect
60 min
Why is GPG "damn near unusable"?
An overview of usable security research
58 min