Search for "Jim" returned 5093 results
61 min
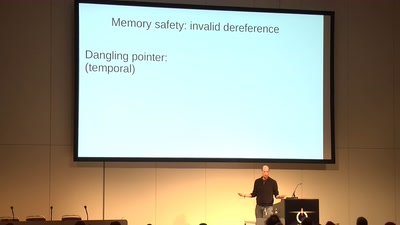
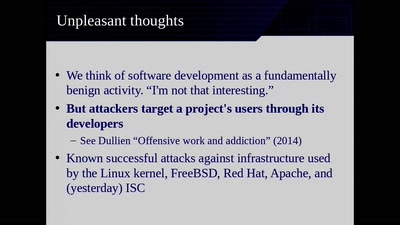
Code Pointer Integrity
... or how we battle the daemons of memory safety
63 min
Reproducible Builds
Moving Beyond Single Points of Failure for Software…
63 min
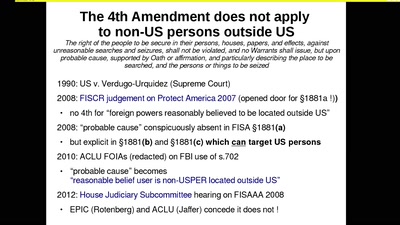
The Cloud Conspiracy 2008-2014
how the EU was hypnotised that the NSA did not exist
60 min
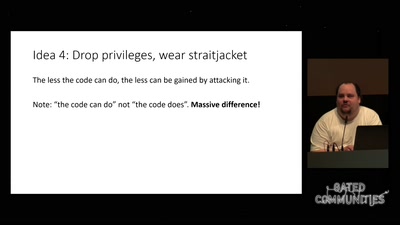
Check your privileges!
How to drop more of your privileges to reduce attack…
54 min
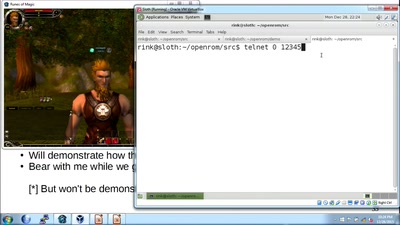
How hackers grind an MMORPG: by taking it apart!
An introduction to reverse engineering network protocols
65 min
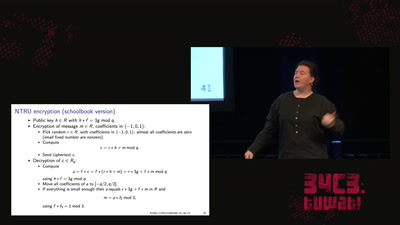
LatticeHacks
Fun with lattices in cryptography and cryptanalysis
56 min
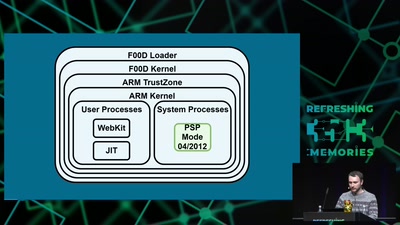
Viva la Vita Vida
Hacking the most secure handheld console

62 min
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
57 min
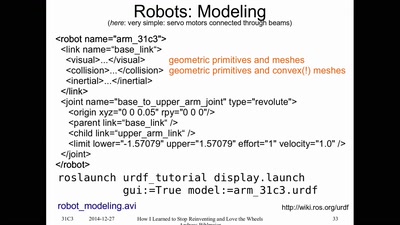
How I Learned to Stop Reinventing and Love the Wheels
or having FUN with (home/hackerspace) robotics
55 min
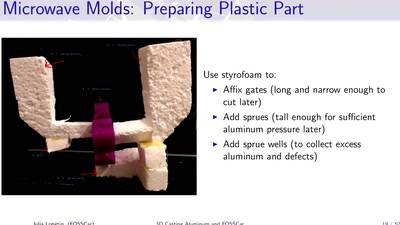
3D Casting Aluminum
Too Much Fun with Microwaves
60 min
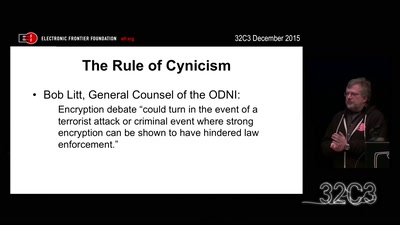
Crypto Wars Part II
The Empires Strike Back
59 min
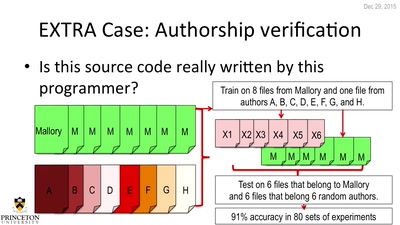
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
61 min