Search for "Jong-Hoon Lee" returned 553 results
61 min
How Alice and Bob meet if they don't like onions
Survey of Network Anonymisation Techniques

59 min
Say hi to your new boss: How algorithms might soon control our lives.
Discrimination and ethics in the data-driven society

61 min
Correcting copywrongs
European copyright reform is finally on the horizon
58 min
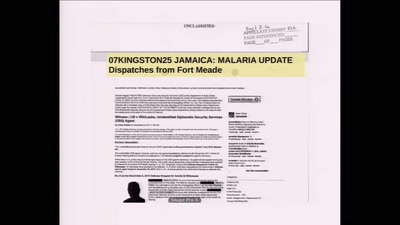
07KINGSTON25 JAMAICA: MALARIA UPDATE Dispatches from Fort Meade
Reporting on the secret trial of Chelsea Manning

58 min
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
58 min
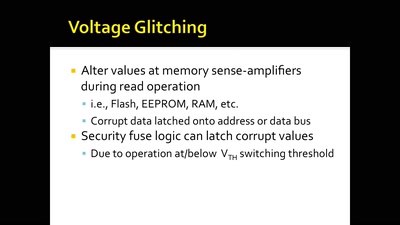
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets

61 min
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…
42 min
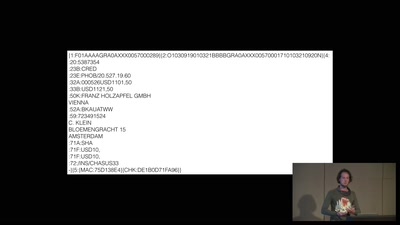
A world without blockchain
How (inter)national money transfers works

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time

60 min
net neutrality: days of future past?
Taking stock after two years of net neutrality in the…

41 min
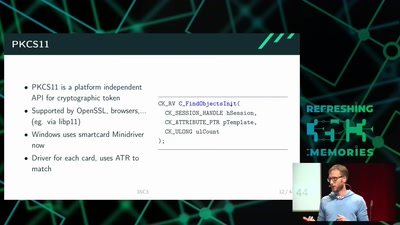
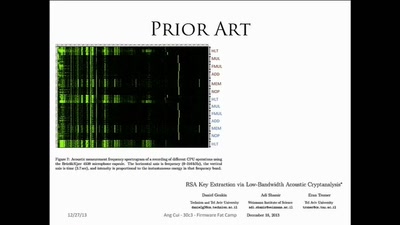
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
58 min
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
38 min
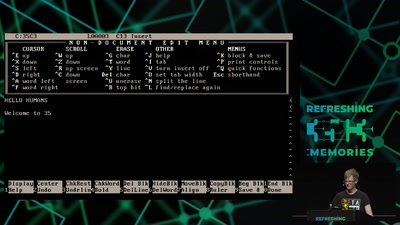
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
42 min
Firmware Fat Camp
Embedded Security Using Binary Autotomy
58 min
Überwachen und Sprache
How to do things with words
47 min