Search for "ALH" returned 6012 results

43 min
Repair-Cafés
… und warum ihr dabei mitmachen solltet
60 min
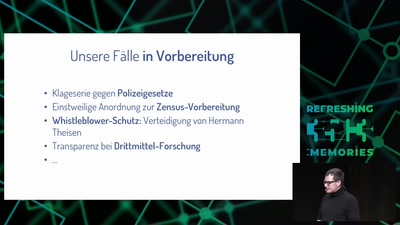
Freedom needs fighters!
Wie die GFF mit strategischen Klagen für Freiheitsrechte…
51 min
The GNU Name System
A Decentralized PKI For Social Movements
63 min
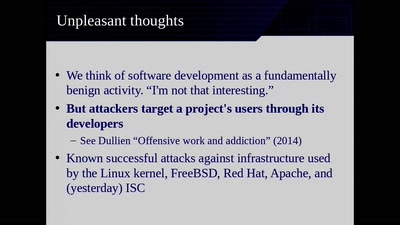
Reproducible Builds
Moving Beyond Single Points of Failure for Software…
64 min
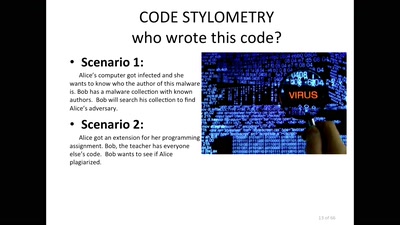
Source Code and Cross-Domain Authorship Attribution
The Role of Stylometry in Privacy
38 min
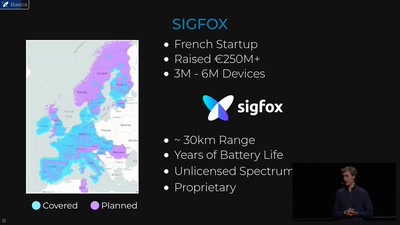
Hunting the Sigfox: Wireless IoT Network Security
Dissecting the radio protocol of Sigfox, the global…

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
47 min
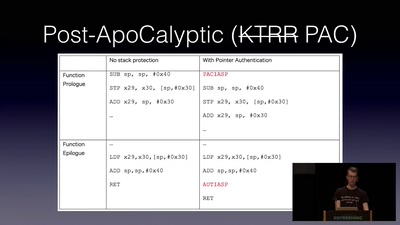
Jailbreaking iOS
From past to present
47 min
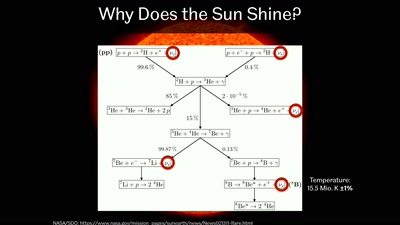
Going Deep Underground to Watch the Stars
Neutrino Astronomy with Hyper-Kamiokande

56 min
Reality Check! Basel/Lagos?? In virtual reality?
An African tale of art, culture and technology
58 min
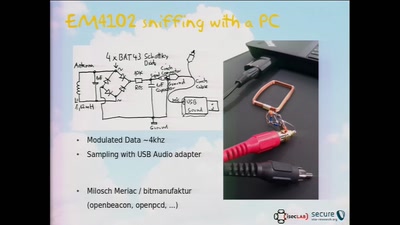
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
30 min
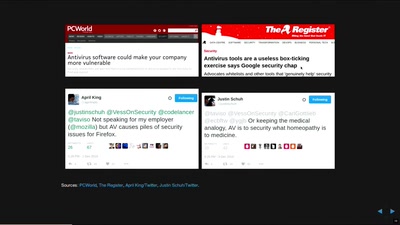
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
29 min
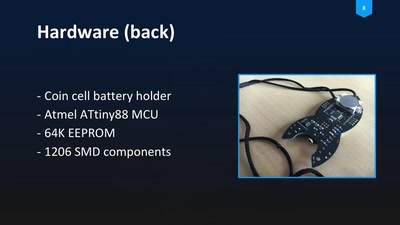
Blinkenrocket!
How to make a community project fly
62 min
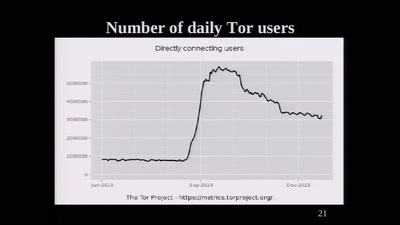
The Tor Network
We're living in interesting times

31 min
Sysadmins of the world, unite!
a call to resistance

26 min