Search for "sECuRE" returned 800 results
58 min
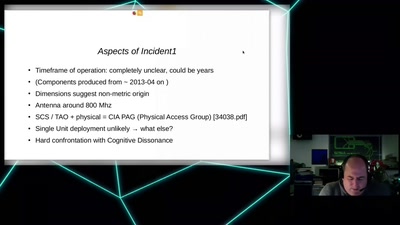
CIA vs. Wikileaks
Intimiditation surveillance and other tactics observed and…

58 min
Uncertain Concern
How Undocumented Immigrants in the US Navigate Technology
58 min
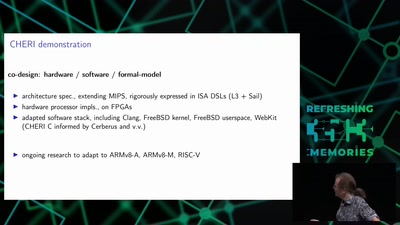
Taming the Chaos: Can we build systems that actually work?
Possible paths from today's ghastly hackery to what…
60 min
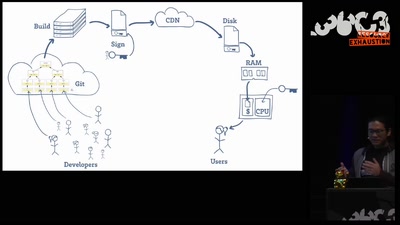
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
63 min
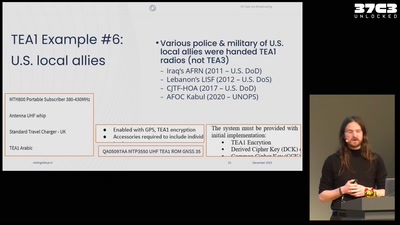
All cops are broadcasting
TETRA unlocked after decades in the shadows
31 min
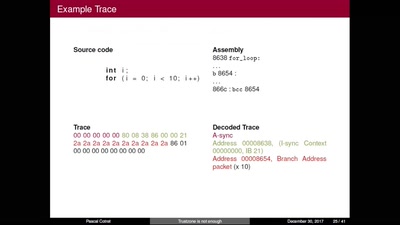
TrustZone is not enough
Hijacking debug components for embedded security

51 min
Funky File Formats
Advanced binary tricks

57 min
Everything you want to know about x86 microcode, but might have been afraid to ask
An introduction into reverse-engineering x86 microcode and…
38 min
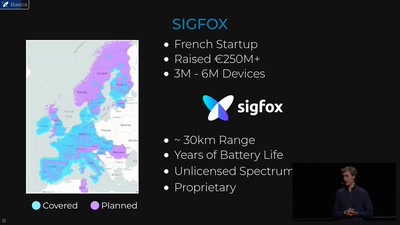
Hunting the Sigfox: Wireless IoT Network Security
Dissecting the radio protocol of Sigfox, the global…
61 min
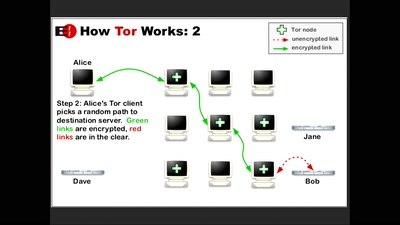
How Alice and Bob meet if they don't like onions
Survey of Network Anonymisation Techniques
32 min