Search for "sECuRE" returned 800 results
61 min
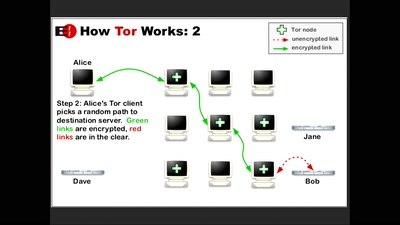
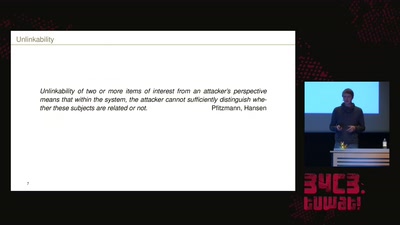
How Alice and Bob meet if they don't like onions
Survey of Network Anonymisation Techniques
32 min
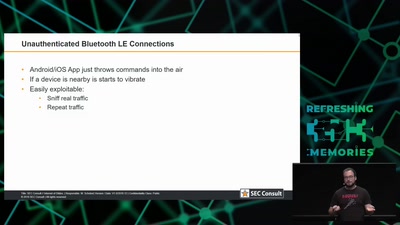
Internet of Dongs
A long way to a vibrant future
30 min
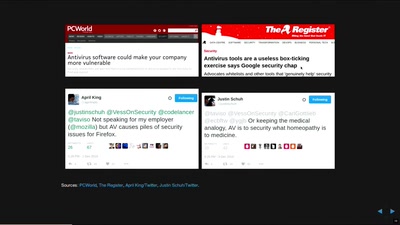
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
41 min
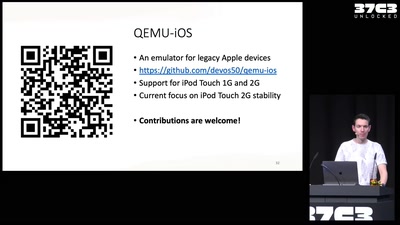
Breathing Life into Legacy: An Open-Source Emulator of Legacy Apple Devices
A Dive into Reverse Engineering and Understanding the iPod…

38 min
Chaospager
How to construct an Open Pager System for c3
56 min
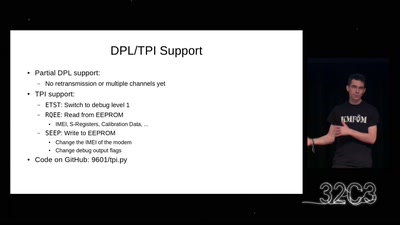
Iridium Update
more than just pagers
58 min
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…

25 min
»Hard Drive Punch«
Destroying data as a performative act

51 min
Digital Identity and Digital Euro
what is the EU up to now?

43 min
Tractors, Rockets and the Internet in Belarus
How belarusian authoritarian regime is using technologies…
38 min
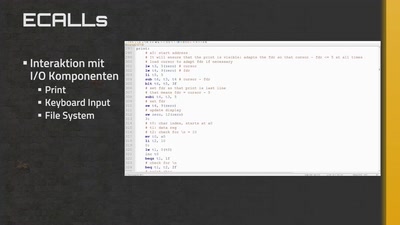
CPU Entwicklung in Factorio
Vom D-Flip-Flop bis zum eigenen Betriebssystem
31 min
PUFs, protection, privacy, PRNGs
an overview of physically unclonable functions
49 min
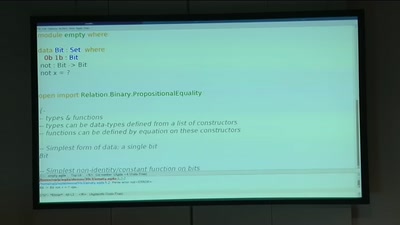
BREACH in Agda
Security notions, proofs and attacks using dependently…
60 min