Search for "tim" returned 6509 results
58 min
Open Source Estrogen
From molecular colonization to molecular collaboration
32 min
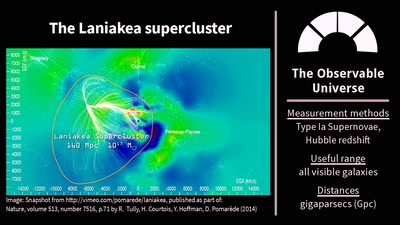
The Universe Is, Like, Seriously Huge
Stuff in Space Is Far Away – but How Do We Know?
45 min
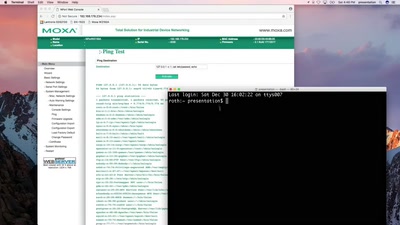
SCADA - Gateway to (s)hell
Hacking industrial control gateways
38 min
ARMore: Pushing Love Back Into Binaries
Aarch64 binary rewriting adventures but mostly pains
33 min
UPSat - the first open source satellite
Going to space the libre way
30 min
All Our Shared Spectrum Are Belong to Us
Visualizing WLAN Channel Usage on OpenWRT

46 min
Maker Spaces in Favelas - Lecture
Engaging social innovation and social innovators
38 min
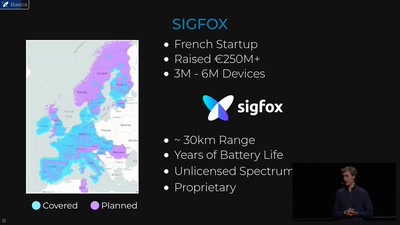
Hunting the Sigfox: Wireless IoT Network Security
Dissecting the radio protocol of Sigfox, the global…
46 min
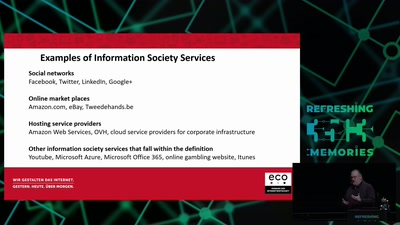
Electronic Evicence in Criminal Matters
An introduction and critique of the EC proposal for a…
60 min
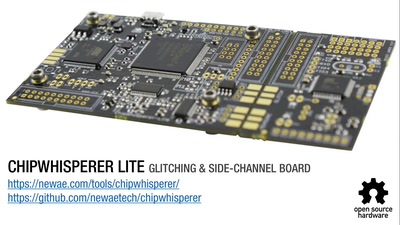
Opening Closed Systems with GlitchKit
'Liberating' Firmware from Closed Devices with Open Source…
61 min
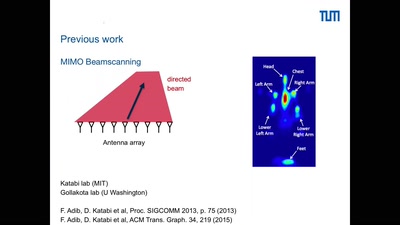
Holography of Wi-Fi radiation
Can we see the stray radiation of wireless devices? And…
20 min
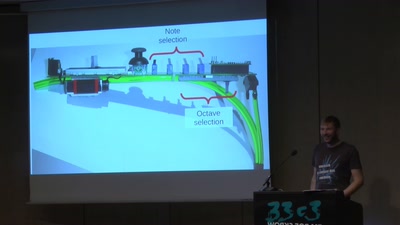
The Nibbletronic
A DIY MIDI Controller and a New UI for Wind Instruments
55 min
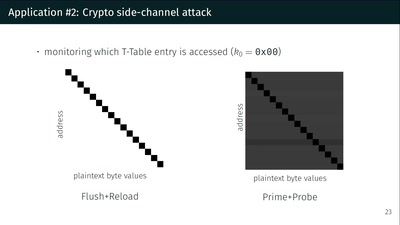
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…
26 min
Der 33 Jahrerückblick
Technology and Politics in Congress Talks, from 1984 to now
31 min
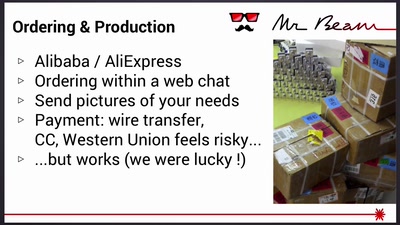
Mr Beam goes Kickstarter
Lessons learned from crowdfunding a hardware project
32 min
Visceral Systems
Approaches to working with sound and network data…

60 min