Search for "ALH" returned 6013 results
63 min
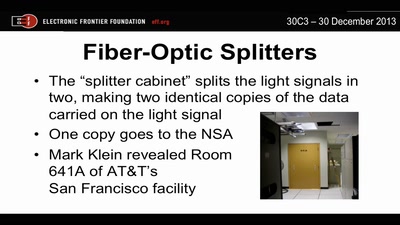
Through a PRISM, Darkly
Everything we know about NSA spying

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
58 min
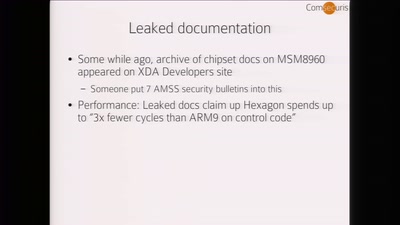
Baseband Exploitation in 2013
Hexagon challenges
59 min
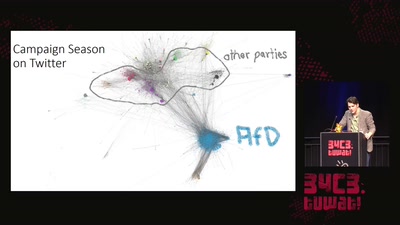
Pointing Fingers at 'The Media'
The Bundestagswahl 2017 and Rise of the AfD
31 min
BGP and the Rule of Custom
How the internet self-governs without international law
60 min
Dieselgate – A year later
env stinks || exit
61 min
Rocket Kitten: Advanced Off-the-Shelf Targeted Attacks Against Nation States
A Deep Technical Analysis
30 min
Automatically Subtitling the C3
How speech processing helps the CCC subtitle project, and…
46 min
You can -j REJECT but you can not hide: Global scanning of the IPv6 Internet
Finding interesting targets in 128bit of entropy
62 min
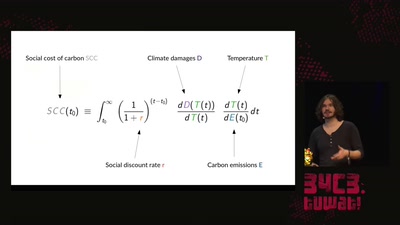
A hacker's guide to Climate Change - What do we know and how do we know it?
An introduction to the basics of climate research and what…
60 min
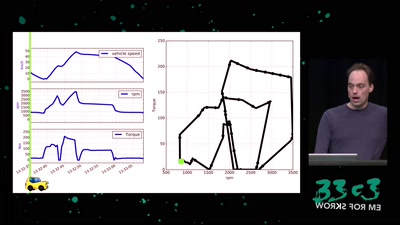
Software Defined Emissions
A hacker’s review of Dieselgate

57 min
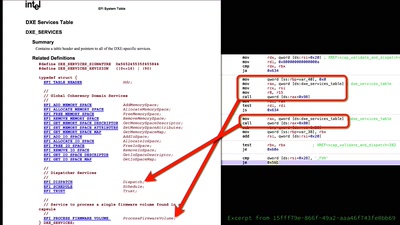
Everything you want to know about x86 microcode, but might have been afraid to ask
An introduction into reverse-engineering x86 microcode and…
32 min