Search for "Andi" returned 7497 results
38 min
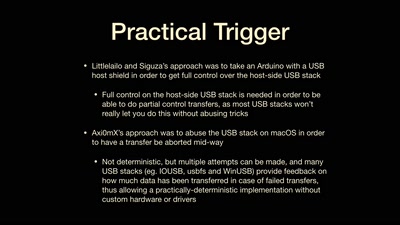
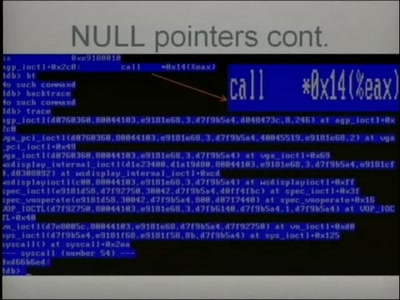
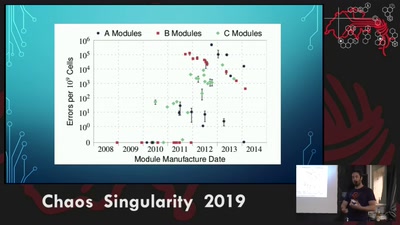
Rowhammer exploit
Viability of the Rowhammer Attack when ECC memory is used
16 min
For Fox’s Sake
Bypassing Enterprise Policy in Firefox
18 min
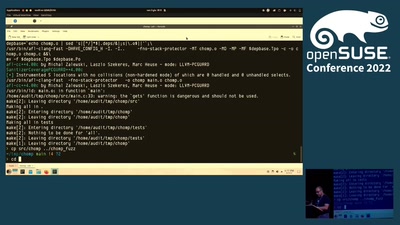
(opensource == secure)? Yes, if you audit it!
Tales in a life of a product security engineer making…
47 min
Power to the Patient
How Crowdsourcing could change Biomedicine

73 min
We lost the war
Welcome to the world of tomorrow
38 min
Squeezing Attack Traces
How to get useable information out of your honeypot

35 min
AllColoursAreBeautiful
interactive light installation inspired by blinkenlights
54 min
The coming war on general computation
The copyright war was just the beginning
49 min
Attacking OpenSSL using Side-channel Attacks
The RSA case study
38 min
Designing a 3D printed tool for medical use
From reverse engineering to iterative design

66 min
COMPLETE Hard Disk Encryption with FreeBSD
Learn how to effectively protect not only your data but…
57 min