Search for "Bea" returned 6255 results

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
31 min
JODI - Apache is functioning normally
A net.art collective since 1995. Understanding the browser…
39 min
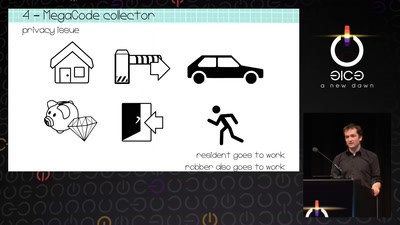
The automobile as massive data gathering source and the consequences for individual…
The next big privacy heist
58 min
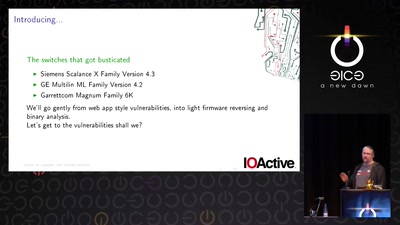
Switches Get Stitches
Industrial System Ownership
33 min
The Transhumanist Paradox
Deciding between technological utopias in a liberal state

56 min
Household, Totalitarianism and Cyberspace
Philosophical Perspectives on Privacy Drawing on the…
46 min
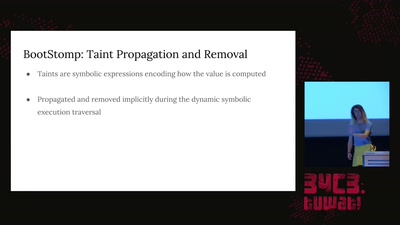
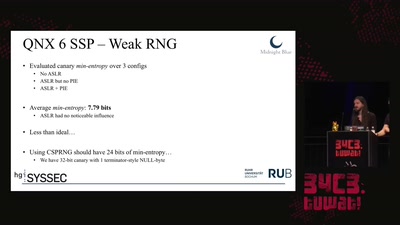
Taking a scalpel to QNX
Analyzing & Breaking Exploit Mitigations and Secure Random…
38 min
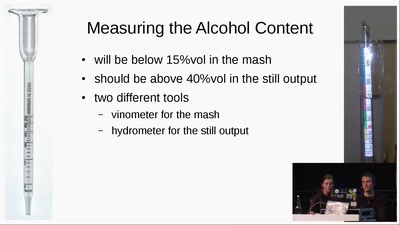
Schnaps Hacking
from apple to schnaps -- a complete diy-toolchain
61 min
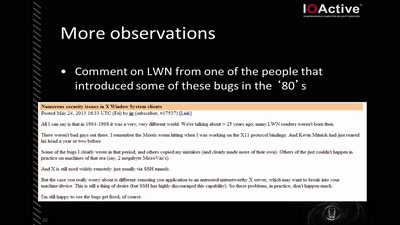
X Security
It's worse than it looks
57 min
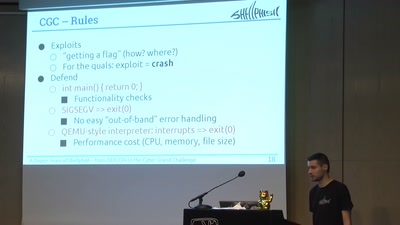
A Dozen Years of Shellphish
From DEFCON to the DARPA Cyber Grand Challenge
51 min
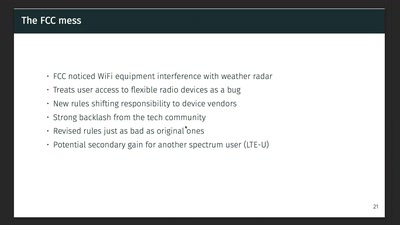
Wireless Drivers: Freedom considered harmful?
An OpenWrt perspective on the development of Linux 802.11…
61 min
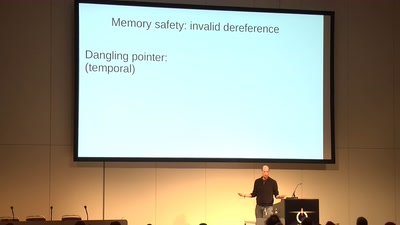
Code Pointer Integrity
... or how we battle the daemons of memory safety
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
59 min
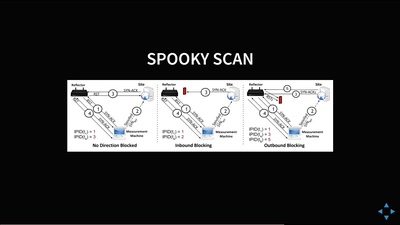
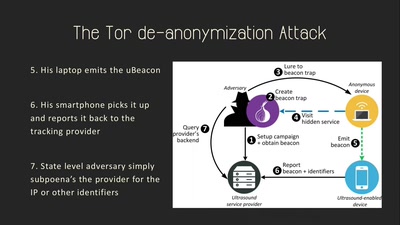
Talking Behind Your Back
On the Privacy & Security of the Ultrasound Tracking…
46 min