Search for "marc" returned 970 results

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
44 min
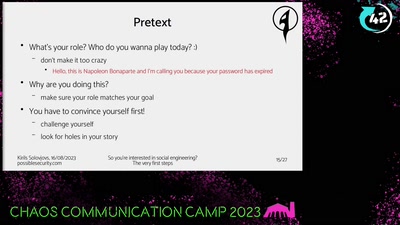
So you're interested in social engineering?
The very first steps
46 min
Writing secure software
using my blog as example
30 min
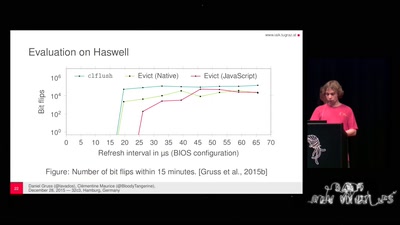
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches
25 min
Saving the World with Space Solar Power
or is it just PEWPEW?!
63 min
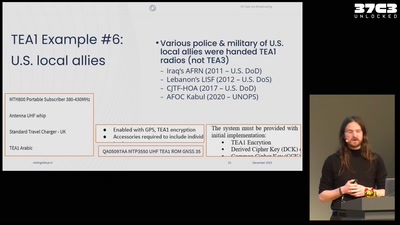
All cops are broadcasting
TETRA unlocked after decades in the shadows
60 min
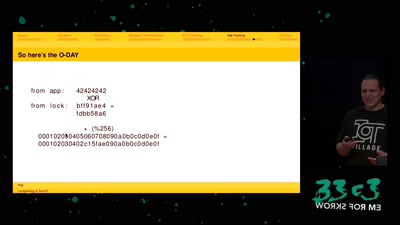
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…

63 min
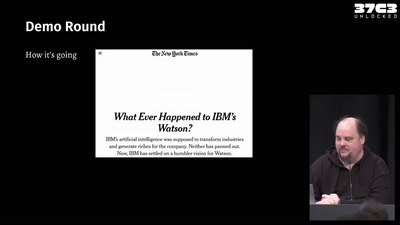
Synthetic Sentience
Can Artificial Intelligence become conscious?
31 min
PUFs, protection, privacy, PRNGs
an overview of physically unclonable functions
59 min