Search for "Leah" returned 1493 results
30 min
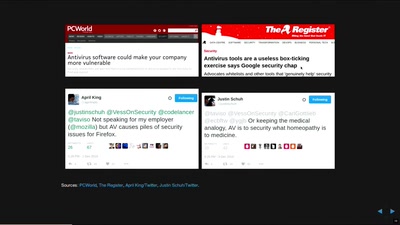
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
41 min
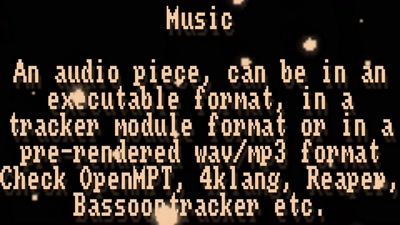
Demoscene now and then
The demoscene is an underground computer art culture.

77 min
Feminist Perspectives
Inclusive and Diverse Spaces and Communities

59 min
Hardsploit: A Metasploit-like tool for hardware hacking
A complete toolbox for IoT security
40 min
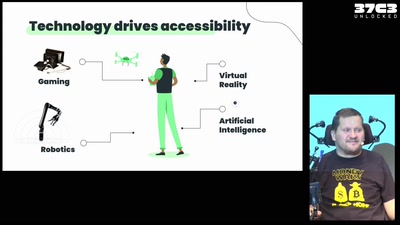
Handsfree assistive technology
My technology portfolio to enable work, life, smart home…
41 min
Why Railway Is Safe But Not Secure
Security Of Railway Communication Protocols
40 min
Fuzz Everything, Everywhere, All at Once
Advanced QEMU-based fuzzing
61 min
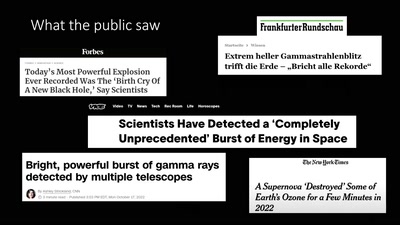
About Gamma-Ray Bursts And Boats
What We (Don't) Know About the Most Energetic Events in the…

31 min
Buffered Daemons
Sound art performance exploring the concept of translation…
53 min
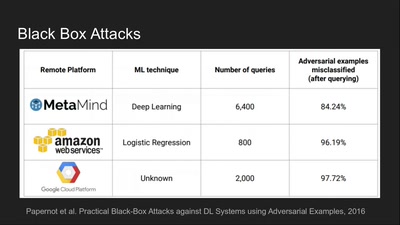
Deep Learning Blindspots
Tools for Fooling the "Black Box"
55 min
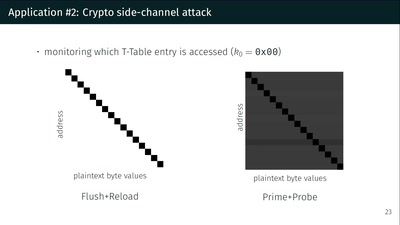
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…
58 min
Open Source Estrogen
From molecular colonization to molecular collaboration

51 min
Funky File Formats
Advanced binary tricks
61 min
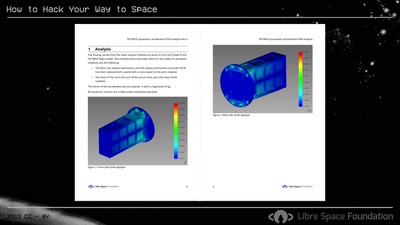
How to Hack Your Way to Space
Bringing the Hacker Mindset to the Space Ecosphere - The…
67 min
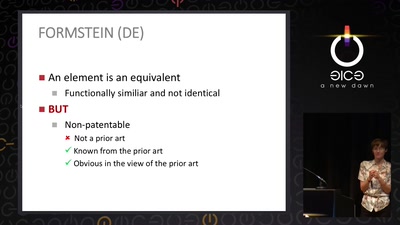
The Maker movement meets patent law
How many windows are open in the patent fortress
37 min