Search for "Matteo" returned 688 results
62 min
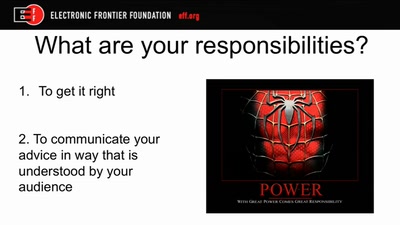
The Internet (Doesn't) Need Another Security Guide
Creating Internet Privacy and Security Resources That Don't…
62 min
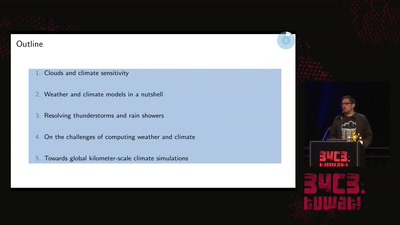
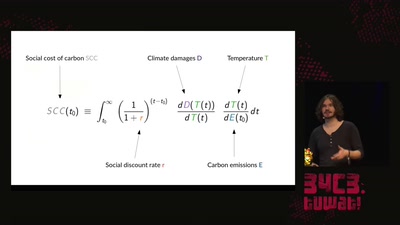
A hacker's guide to Climate Change - What do we know and how do we know it?
An introduction to the basics of climate research and what…
60 min
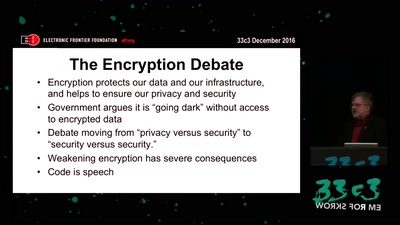
The Fight for Encryption in 2016
Crypto fight in the Wake of Apple v. FBI
58 min
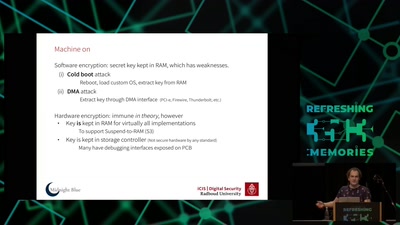
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
44 min
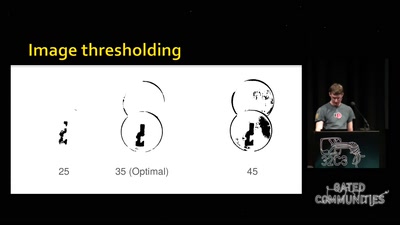
Replication Prohibited
3D printed key attacks
59 min
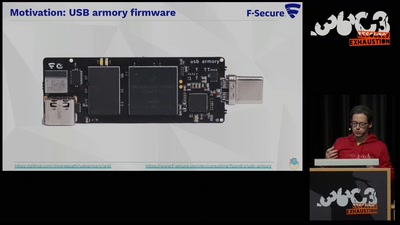
TamaGo - bare metal Go framework for ARM SoCs.
Reducing the attack surface with pure embedded Go.
60 min
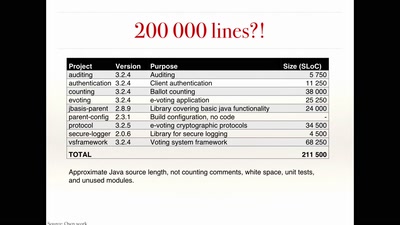
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation
64 min
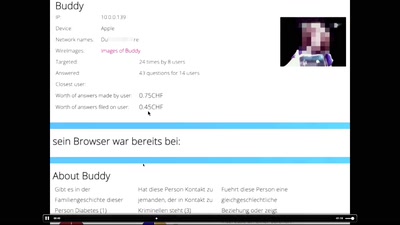
"Exploit" in theater
post-existentialism is the question, not post-privacy
60 min
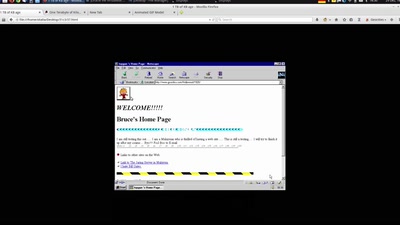
The Only Thing We Know About Cyberspace Is That Its 640x480
One Terabyte of Kilobyte Age
58 min
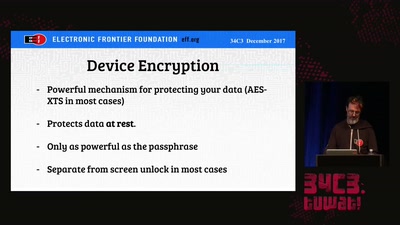
Protecting Your Privacy at the Border
Traveling with Digital Devices in the Golden Age of…
61 min
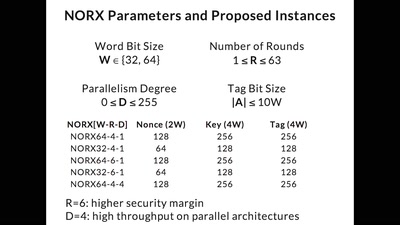
CAESAR and NORX
Developing the Future of Authenticated Encryption
60 min
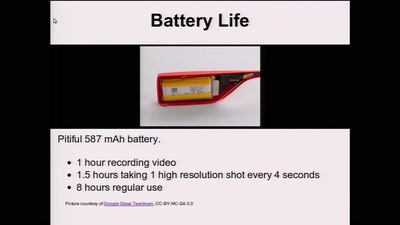
Glass Hacks
Fun and frightening uses of always-on camera enabled…
55 min
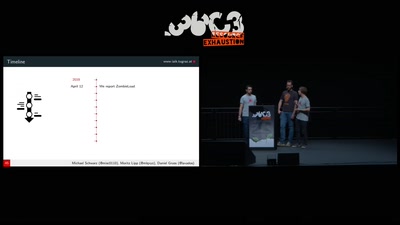
ZombieLoad Attack
Leaking Your Recent Memory Operations on Intel CPUs
55 min