Search for "Andi Rüther" returned 725 results
61 min
Untrusting the CPU
A proposal for secure computing in an age where we cannot…

62 min
To Protect And Infect, Part 2
The militarization of the Internet
64 min
Source Code and Cross-Domain Authorship Attribution
The Role of Stylometry in Privacy
62 min
Bionic Ears
Introduction into State-of-the-Art Hearing Aid Technology
58 min
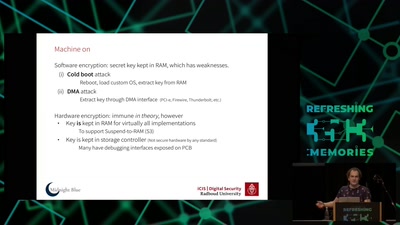
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
58 min
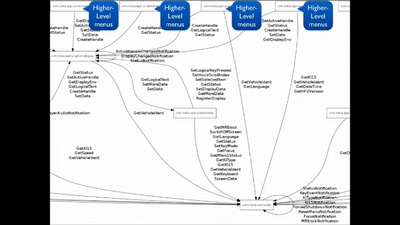
Script Your Car!
Using existing hardware platforms to integrate python into…
61 min
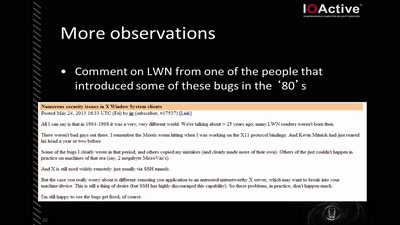
X Security
It's worse than it looks

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
60 min
Low Cost High Speed Photography
Using microcontrollers to capture the blink of an eye for…
65 min
Rocket science – how hard can it be?
First steps into space with sounding rockets

62 min
Space Hacker
Uploading rover...

59 min
Free Electron Lasers
...or why we need 17 billion Volts to make a picture.
113 min