Search for "Olga" returned 131 results
41 min
Österreich: Überwachungsstaat oder doch nur Digitalisierung für Anfänger?
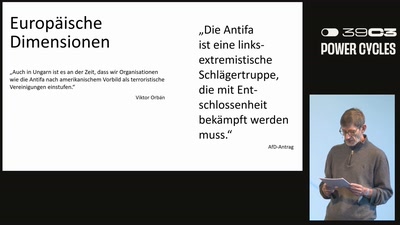
Ein Jahr unter der rechtsextremen Regierung
58 min
selbstverständlich antifaschistisch!
Aktuelle Informationen zu den Verfahren im Budapest-Komplex…
71 min
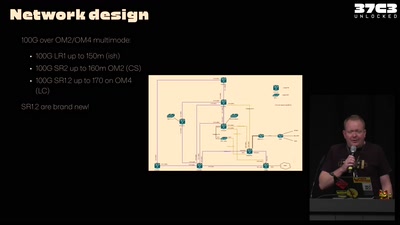
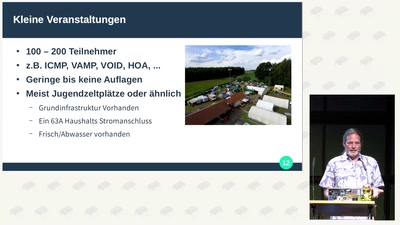
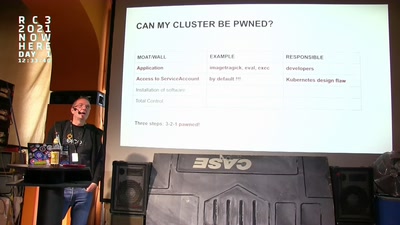
37C3 Infrastructure Review
Teams presenting how they helped making this awesome event
40 min
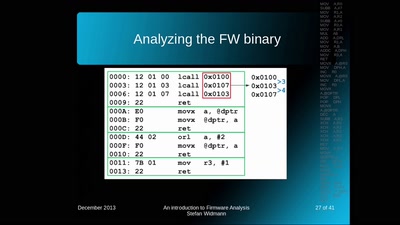
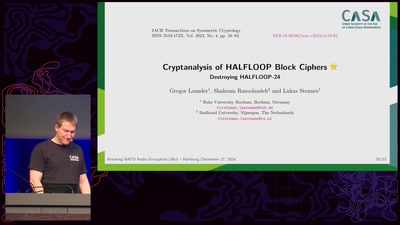
An introduction to Firmware Analysis
Techniques - Tools - Tricks

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
63 min
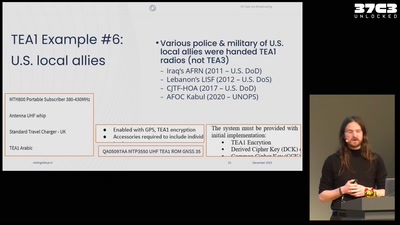
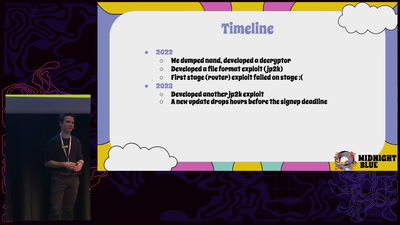
All cops are broadcasting
TETRA unlocked after decades in the shadows

46 min
![Beyond Cryptopartys - wie Aktivistis, [*] und Nerds voneinander lernen können](https://static.media.ccc.de/media/conferences/eh2025/75-d63c05b8-bbcd-5a9a-8488-cb14b538ec72.jpg)