Search for "Paul May" returned 188 results
41 min
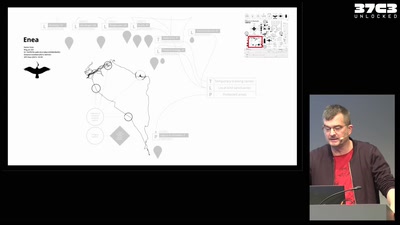
Infrastructure of a migratory bird
Technology and autonomy in more-than-human networks
39 min
DISNOVATION.ORG
Disobedient Innovation
58 min
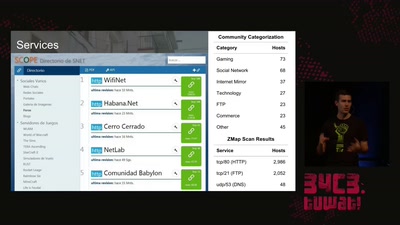
The Internet in Cuba: A Story of Community Resilience
Get a unique tour of some of the world’s most unusual…

29 min
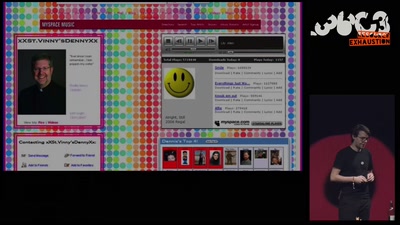
Perfect Paul
On Freedom of Facial Expression
19 min
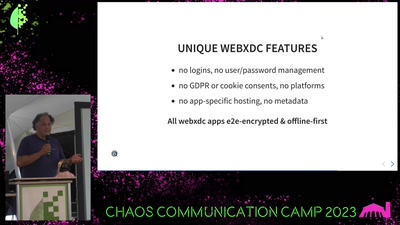
Delta Chat messenger
unlocking the potential of e-mail and the web
41 min
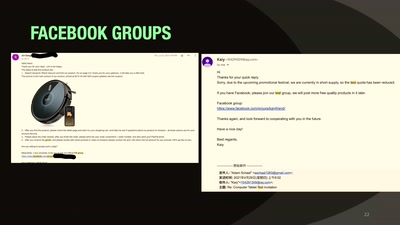
Our Time in a Product Review Cabal
And the malware and backdoors that came with it.

43 min
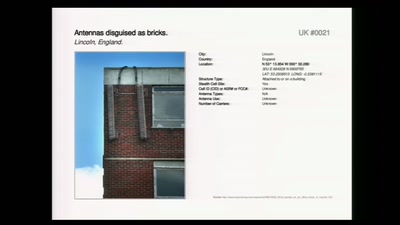
This is NOT a proposal about mass surveillance!
Analysing the terminology of the UK’s Snooper’s Charter
59 min
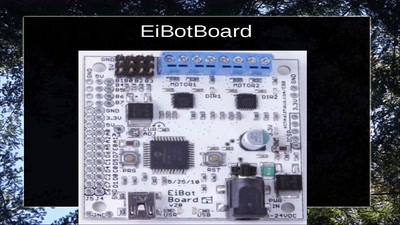
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
47 min
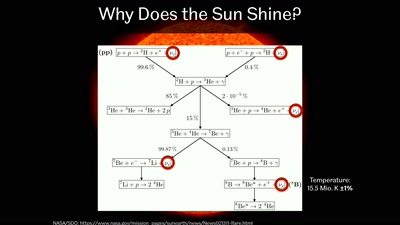
Going Deep Underground to Watch the Stars
Neutrino Astronomy with Hyper-Kamiokande

63 min
The Global Assassination Grid
The Infrastructure and People behind Drone Killings
58 min
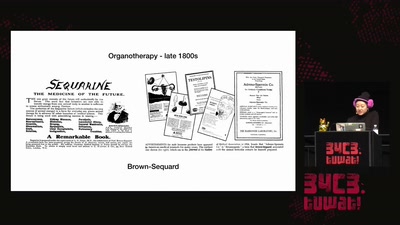
Open Source Estrogen
From molecular colonization to molecular collaboration
30 min
All Our Shared Spectrum Are Belong to Us
Visualizing WLAN Channel Usage on OpenWRT
55 min
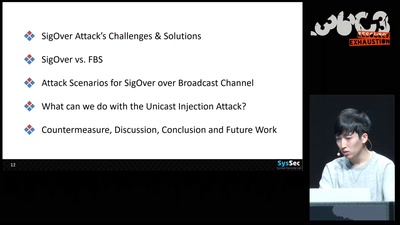
SigOver + alpha
Signal overshadowing attack on LTE and its applications
58 min
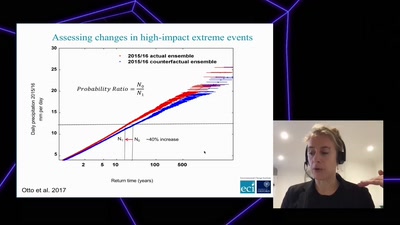
Angry weather ?
How human-induced climate change affects weather (& how we…

62 min
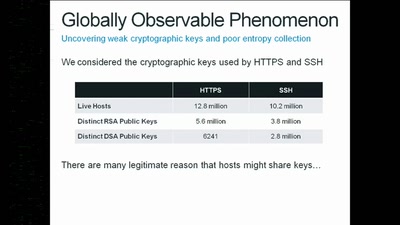
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
47 min
Hillbilly Tracking of Low Earth Orbit
Repurposing an Inmarsat Dish

32 min
Craft, leisure, and end-user innovation
How hacking is conceived in social science research
37 min