Search for "Hugo" returned 788 results
55 min
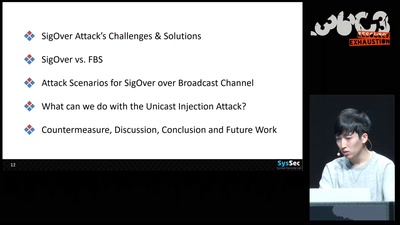
SigOver + alpha
Signal overshadowing attack on LTE and its applications
54 min
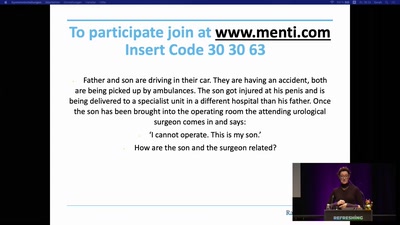
How medicine discovered sex
Introduction to sex- and gender-sensitive medicine
58 min
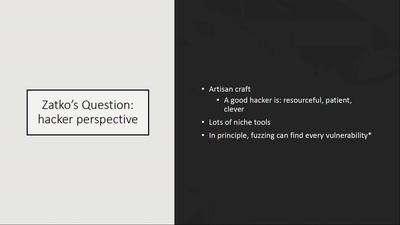
How risky is the software you use?
CITL: Quantitative, Comparable Software Risk Reporting

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
67 min
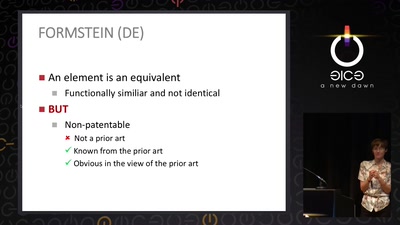
The Maker movement meets patent law
How many windows are open in the patent fortress
58 min
CHINTERNET ART
Creativity, Archives & Digital Media from the Chinese…

59 min
Hardsploit: A Metasploit-like tool for hardware hacking
A complete toolbox for IoT security
61 min
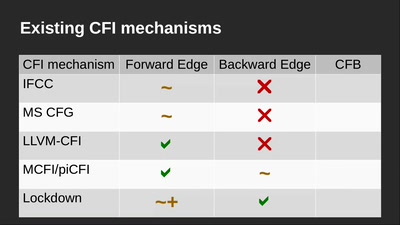
Code Pointer Integrity
... or how we battle the daemons of memory safety
50 min
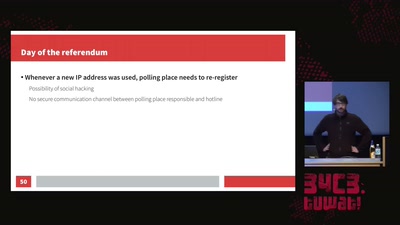
Internet censorship in the Catalan referendum
Overview of how the state censored and how it got…
53 min
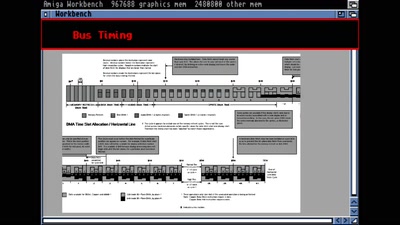
The Ultimate Amiga 500 Talk
Amiga Hardware Design And Programming

51 min
Funky File Formats
Advanced binary tricks
50 min
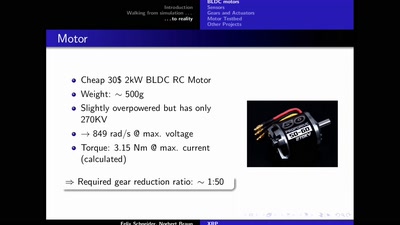
The eXperimental Robot Project
An open-hardware bipedal walking machine

53 min
No Love for the US Gov.
Why Lauri Love’s case is even more important than you…
58 min
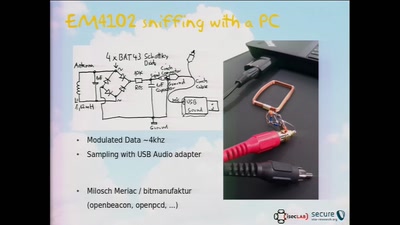
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
54 min
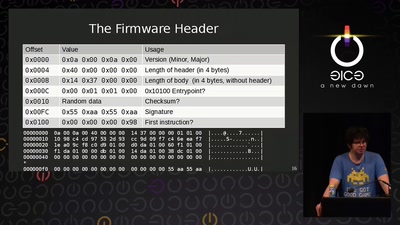
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?
48 min
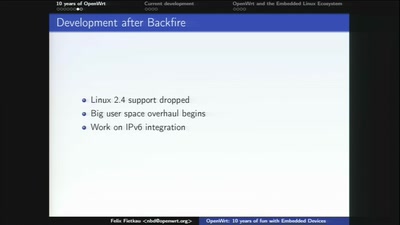
10 Years of Fun with Embedded Devices
How OpenWrt evolved from a WRT54G firmware to an universal…
44 min
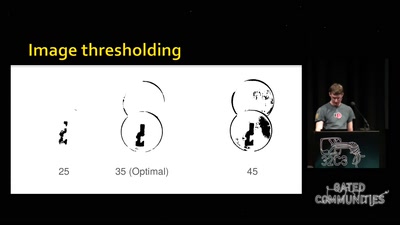
Replication Prohibited
3D printed key attacks
44 min