Search for "Jean" returned 1497 results

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
33 min
Turing Complete User
What can be done to protect the term, the notion and the…
31 min
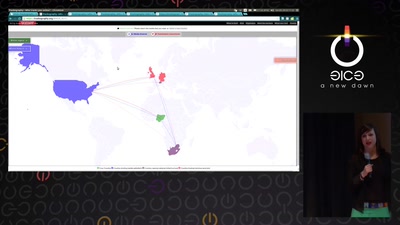
Trackography
You never read alone
57 min
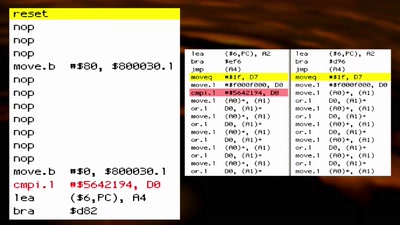
The Layman's Guide to Zero-Day Engineering
A demystification of the exploit development lifecycle
38 min
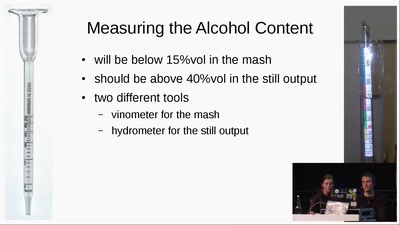
Schnaps Hacking
from apple to schnaps -- a complete diy-toolchain
46 min
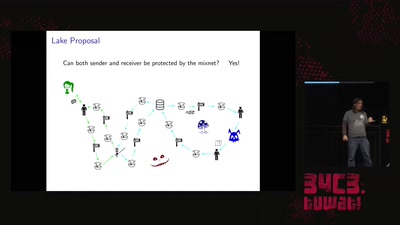
Practical Mix Network Design
Strong metadata protection for asynchronous messaging
60 min
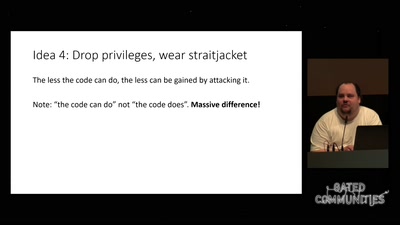
Check your privileges!
How to drop more of your privileges to reduce attack…
60 min
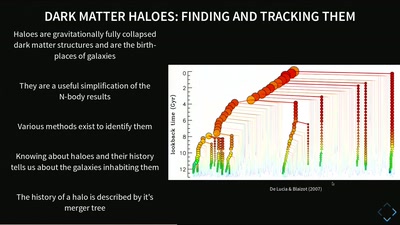
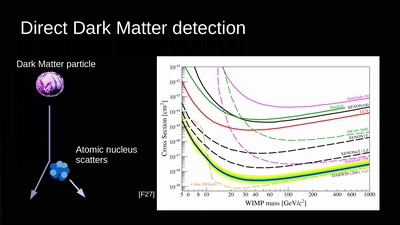
Simulating Universes
What Virtual Universes Can Tell Us About Our Own
49 min
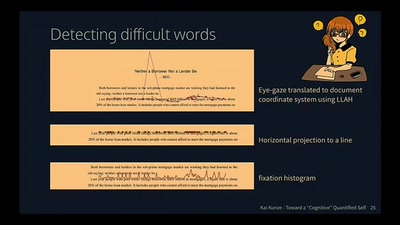
Toward a Cognitive "Quantified Self"
Activity Recognition for the Mind
25 min
Saving the World with Space Solar Power
or is it just PEWPEW?!
39 min
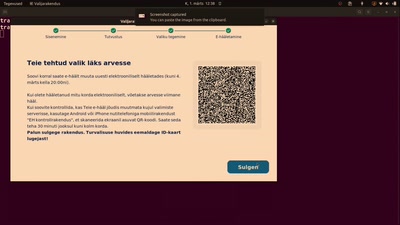
Should e-voting experience of Estonia be copied?
Observer report of 2023 parliamentary elections
30 min
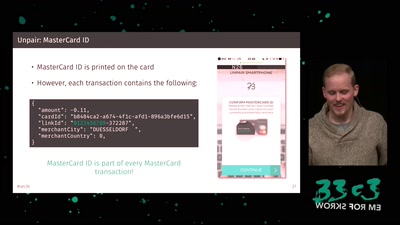
Shut Up and Take My Money!
The Red Pill of N26 Security

33 min
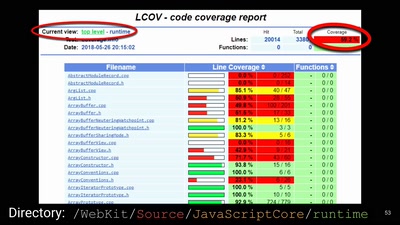
Gone in 60 Milliseconds
Intrusion and Exfiltration in Server-less Architectures

42 min
Citzens or subjects? The battle to control our bodies, speech and communications
A call to action to defend our ePrivacy and eliminate…
21 min
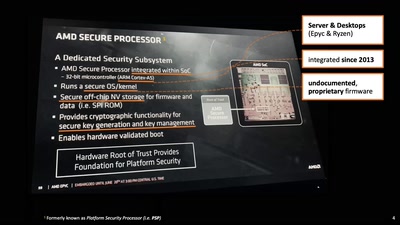
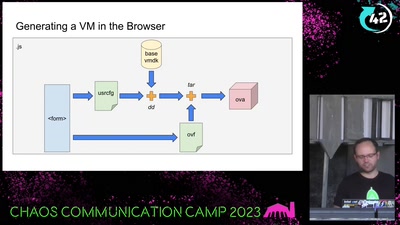
Bootloader Crimes
Building disposable Windows VMs
60 min