Search for "fin" returned 12240 results
48 min
Lücken in der technischen Selbstverteidigung
Open the Blackbox, Close the Bugdoor
64 min
What is in a name?
Identity-Regimes from 1500 to the 2000s
56 min
Rootkits in your Web application
Achieving a permanent stealthy compromise of user accounts…
52 min
Adventures in Mapping Afghanistan Elections
The story of 3 Ushahidi mapping and reporting projects.
19 min
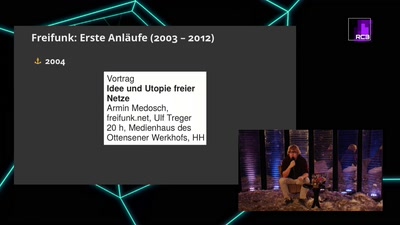
Drölf Jahre Freifunk in Hamburg
Freie WLANs in Hamburg. Ein Rückblick und Ausblick
91 min
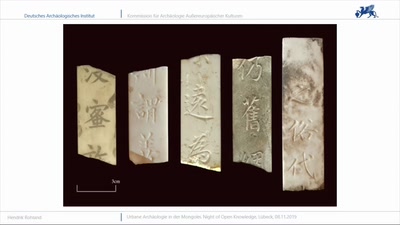
Urbane Archäologie in der Mongolei
Archäologische Forschungen in den alten Hauptstädten der…
62 min
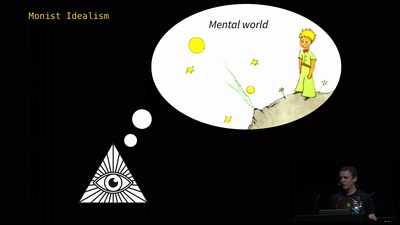
The Ghost in the Machine
An Artificial Intelligence Perspective on the Soul
45 min
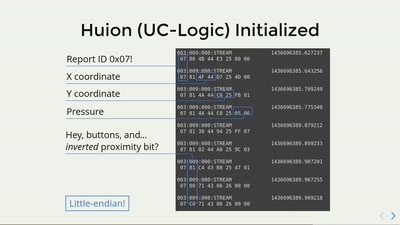
Generic Graphics Tablets in Linux
Hardware peculiarities, software challenges, and how to…
36 min
Mycroft: A.I. in the desktop
Control your desktop with your voice
51 min
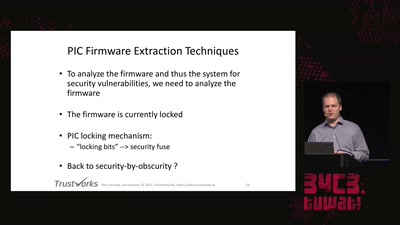
Uncovering vulnerabilities in Hoermann BiSecur
An AES encrypted radio system
53 min
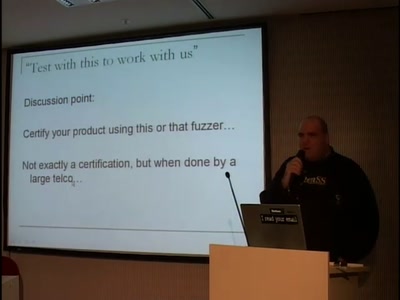
Fuzzing in the corporate world
The use of fuzzing in the corporate world over the years…

46 min
Automated Exploit Detection in Binaries
Finding exploitable vulnerabilities in binaries
59 min