Search for "sECuRE" returned 800 results

39 min
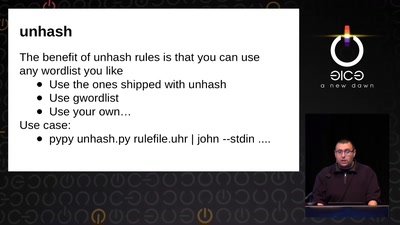
The Eye on the Nile
Egypt's Civil Society Under Attack
42 min
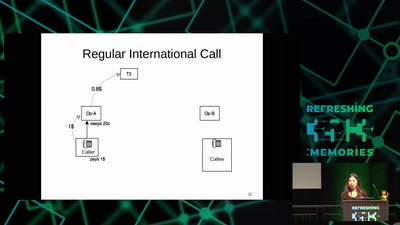
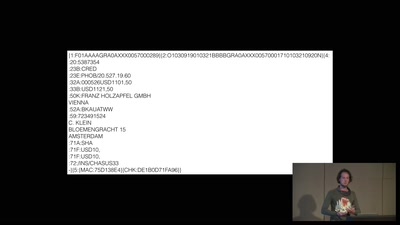
A world without blockchain
How (inter)national money transfers works
60 min
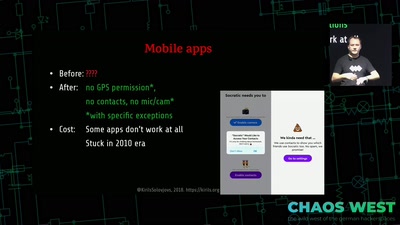
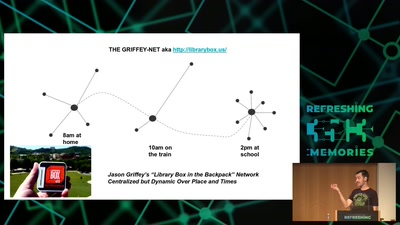
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…
60 min
Lets break modern binary code obfuscation
A semantics based approach
64 min
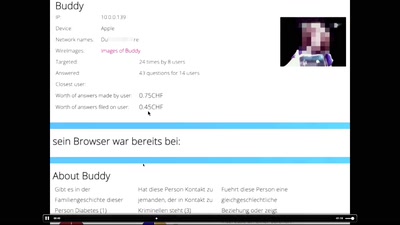
"Exploit" in theater
post-existentialism is the question, not post-privacy
57 min
The Layman's Guide to Zero-Day Engineering
A demystification of the exploit development lifecycle
32 min
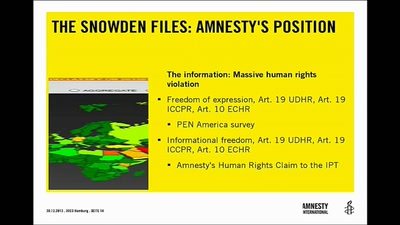
Human Rights and Technology
"A New Hope" or "The Empire Strikes Back"?

46 min
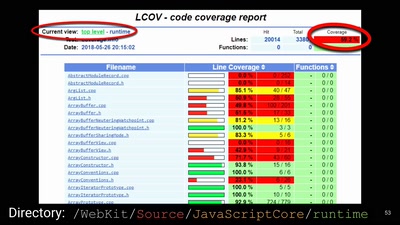
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
58 min
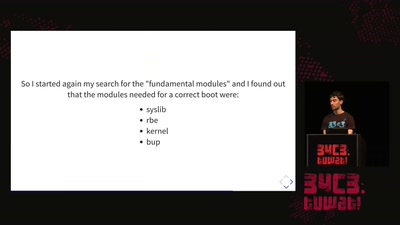
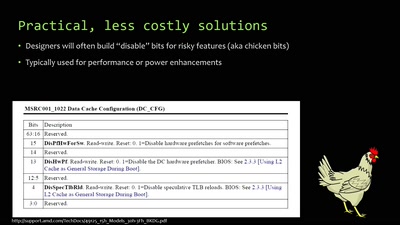
When hardware must „just work“
An inside look at x86 CPU design

63 min
Dissecting HDMI
Developing open, FPGA-based capture hardware for conference…

53 min
No Love for the US Gov.
Why Lauri Love’s case is even more important than you…
58 min