Search for ">Y<" returned 10967 results
29 min
SHA2017 Closing
Five days of hacking, this is what happened. You wouldn't…
34 min
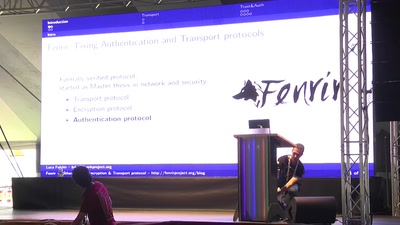
The Fenrir Project
Fixing Authentication and Transport protocols

36 min
Parkour communications
How you can communicate, free running style, using nothing…
61 min
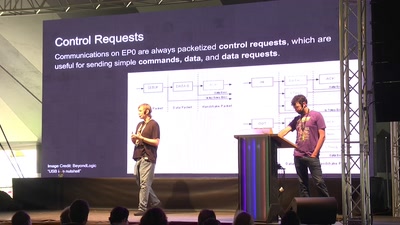
FaceDancer 2.0
easy USB hacking, sniffing, and spoofing
56 min
Hack-a-ble
Hacking BLE Smart Devices

25 min
Hackerspaces Jedi
Everything is interconnected - but how?
54 min
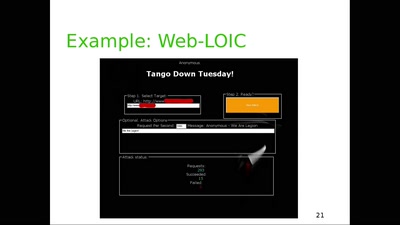
DDoS attack and defense
for the lulz
![NSFW: Di[CENSORED]s for privacy](https://static.media.ccc.de/media/events/SHA2017/49-hd.jpg)
28 min
NSFW: Di[CENSORED]s for privacy
Why not give hackers and agencies something to look at . .

57 min
Biometric ID cards by the billion
Experiences with Aadhaar in India, or what possibly could…

44 min
Life Needs Internet
Documenting digital culture through handwritten letters

61 min
Resisting Algorithms of Mass Destruction
#NotMyDebt Australia
49 min
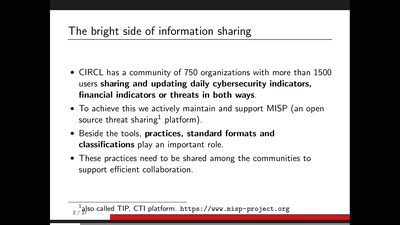
MISP threat sharing platform
The MISP threat sharing platform is a free and open source…
17 min
"Information. What are they looking at?"
A documentary on privacy for the broad audience.

41 min
Ask your candidates and let everyone know about it
How to make use of democratic elections for your own purpose
24 min
Responsible Disclosure; How to make your school a safer place.
Story of a 15 year old hacker in collaboration with his…
60 min
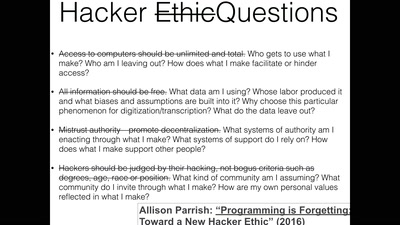
Ethics in Technology
Internet Measurements' Ethical Dilemmas and RIPE Atlas
26 min
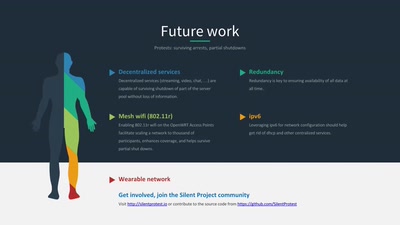
Silent Protest
DIY wearable protest network
49 min
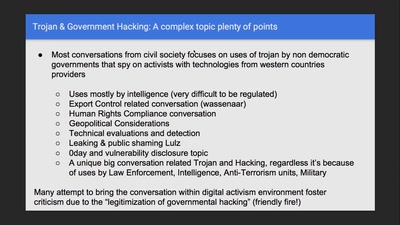
Regulating Law Enforcement use of Trojans
Implementing a Law to juridically, operationally and…
30 min
Gems are truly outrageous
Combining 3D printing and crystallisation techniques
51 min
Playing defence is complicated
What goes into playing defence and what can be holding you…
35 min