Search for "Steff" returned 1157 results

47 min
Digitalcourage und die Post DHL Group
eine Chronik
56 min
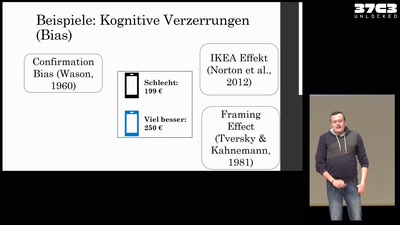
Social Engineering: Geschichte, Wirkung & Maßnahmen.
Alles, was ihr immer über Social Engineering wissen…
32 min
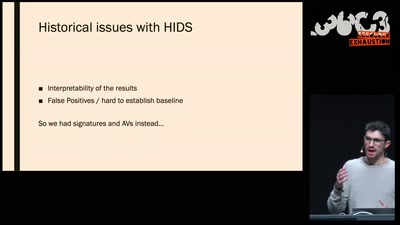
The Case for Scale in Cyber Security
Security Track Keynote
67 min
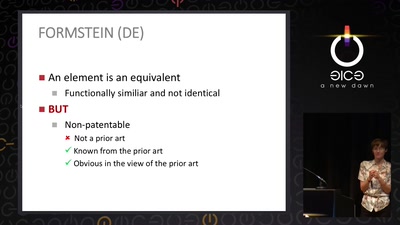
The Maker movement meets patent law
How many windows are open in the patent fortress
51 min
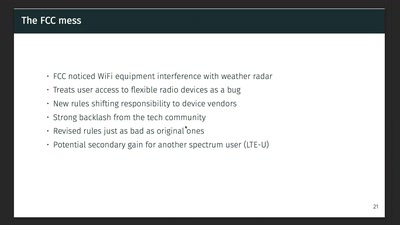
Wireless Drivers: Freedom considered harmful?
An OpenWrt perspective on the development of Linux 802.11…
43 min
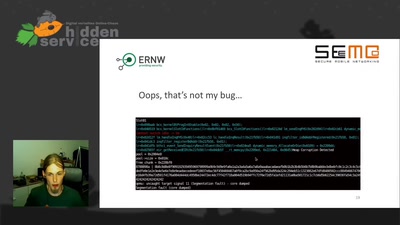
No PoC? No Fix! - A sad Story about Bluetooth Security
It is just a broken memcpy in the Bluetooth stack. Do we…
59 min
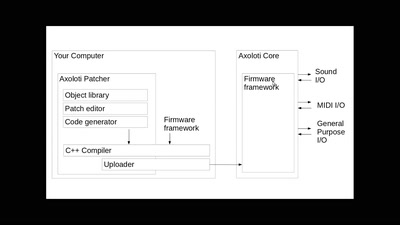
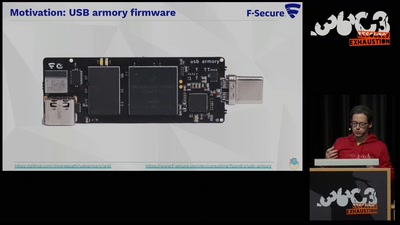
TamaGo - bare metal Go framework for ARM SoCs.
Reducing the attack surface with pure embedded Go.
41 min
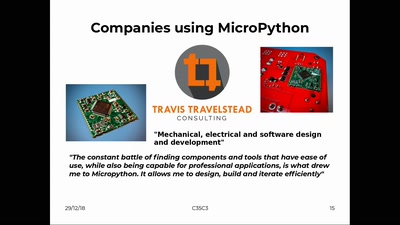
MicroPython – Python for Microcontrollers
How high-level scripting languages make your hardware…
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
53 min
Million Dollar Dissidents and the Rest of Us
Uncovering Nation-State Mobile Espionage in the Wild
60 min
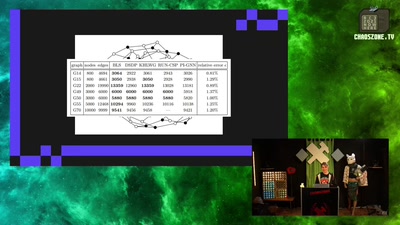
Adventures in Reverse Engineering Broadcom NIC Firmware
Unlocking a system with 100% open source firmware
56 min
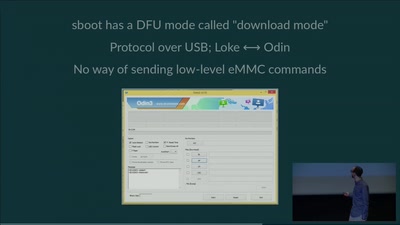
eMMC hacking, or: how I fixed long-dead Galaxy S3 phones
A journey on how to fix broken proprietary hardware by…

33 min
Open source experimental incubator build up
call for participation in project and product development
30 min
Automatically Subtitling the C3
How speech processing helps the CCC subtitle project, and…
48 min
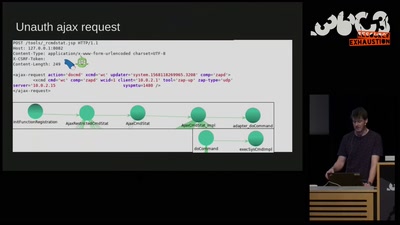
Don't Ruck Us Too Hard - Owning Ruckus AP Devices
3 different RCE vulnerabilities on Ruckus Wireless access…
31 min
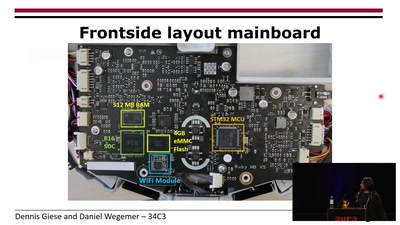
Unleash your smart-home devices: Vacuum Cleaning Robot Hacking
Why is my vacuum as powerful as my smartphone?
56 min