Search for "t" returned 10695 results
61 min
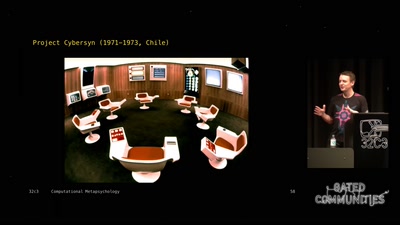
Computational Meta-Psychology
An Artificial Intelligence exploration into the creation of…
60 min
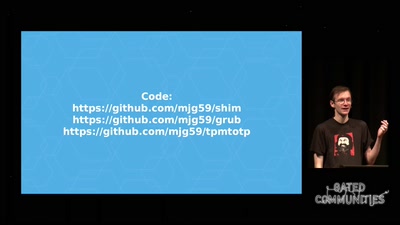
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…
63 min
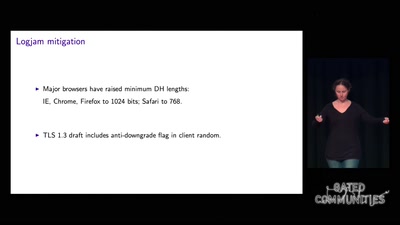
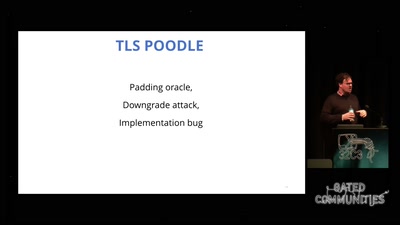
goto fail;
exploring two decades of transport layer insecurity
43 min
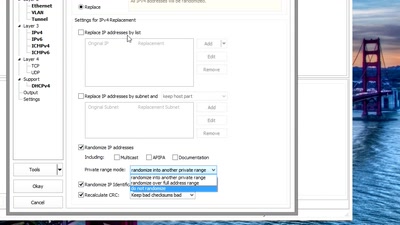
Sanitizing PCAPs
Fun and games until someone uses IPv6 or TCP
56 min
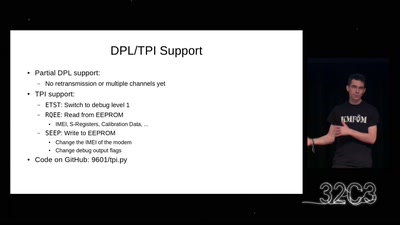
Iridium Update
more than just pagers
60 min
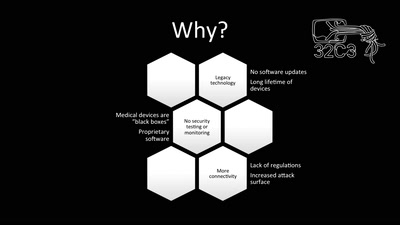
Unpatchable
Living with a vulnerable implanted device
54 min
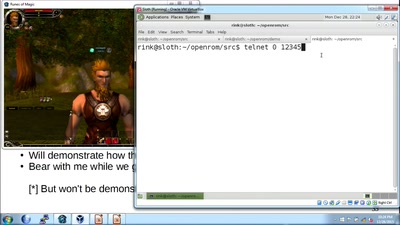
How hackers grind an MMORPG: by taking it apart!
An introduction to reverse engineering network protocols
49 min
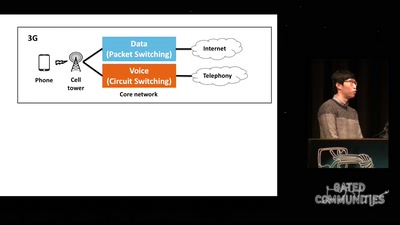
Dissecting VoLTE
Exploiting Free Data Channels and Security Problems

61 min
Quantenphysik und Kosmologie
Eine Einführung für blutige Anfänger

60 min
Das Zahnrad aus Fleisch
Expeditionen ins Kommentierreich
60 min
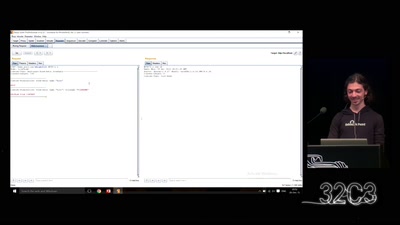
The Perl Jam 2
The Camel Strikes Back

60 min
Quantum Cryptography
from key distribution to position-based cryptography
51 min
Ecuador: how an authoritarian government is fooling the entire world
Guess what? The Government of Rafael Correa actually is…
34 min
Ling - High level system programming
modular and precise resource management
30 min
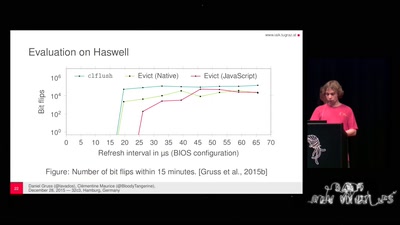
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches
60 min
G’scheitern
The art of failure taught by improv theatre

32 min
Verified Firewall Ruleset Verification
Math, Functional Programming, Theorem Proving, and an…
30 min