Search for "C B" returned 9732 results
59 min
International Cyber Jurisdiction
Kill Switching” Cyberspace, Cyber Criminal Prosecution &…
36 min
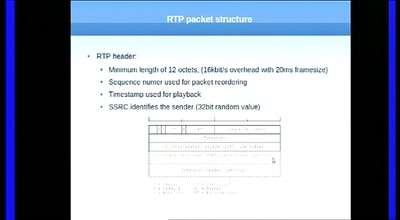
Having fun with RTP
„Who is speaking???“
64 min
Tor is Peace, Software Freedom is Slavery, Wikipedia is Truth
The political philosophy of the Internet
50 min
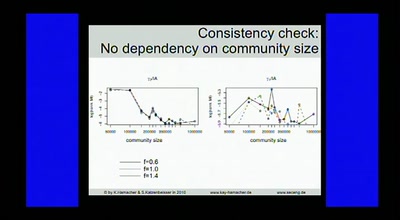
Data Analysis in Terabit Ethernet Traffic
Solutions for monitoring and lawful interception within a…
58 min
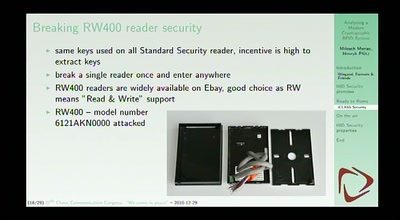
Analyzing a modern cryptographic RFID system
HID iClass demystified
134 min
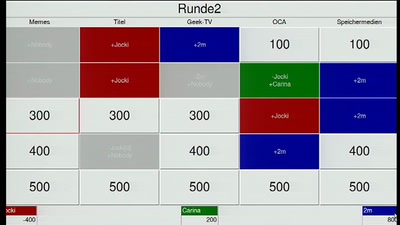
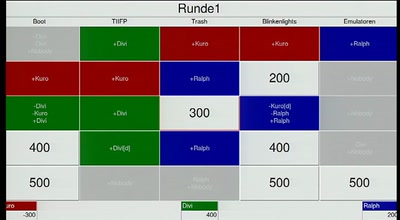
Hacker Jeopardy
Number guessing for geeks
59 min
Safety on the Open Sea
Safe navigation with the aid of an open sea chart.

55 min
FrozenCache
Mitigating cold-boot attacks for Full-Disk-Encryption…
61 min
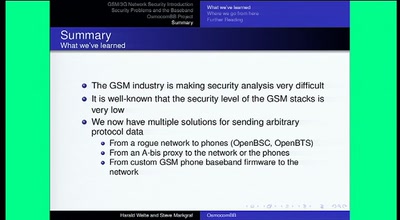
Running your own GSM stack on a phone
Introducing Project OsmocomBB
58 min
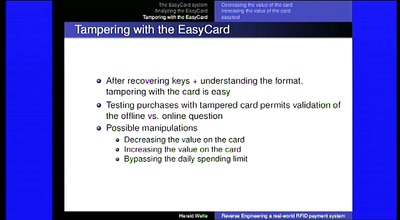
Reverse Engineering a real-world RFID payment system
Corporations enabling citizens to print digital money
63 min
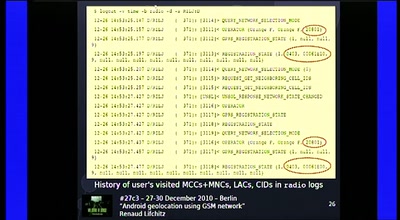
Android geolocation using GSM network
"Where was Waldroid?"
134 min
Hacker Jeopardy (english translation)
Number guessing for geeks
65 min
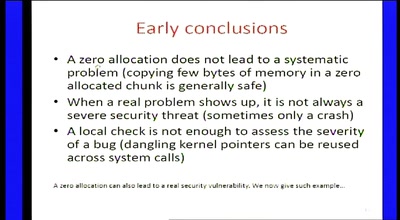
Zero-sized heap allocations vulnerability analysis
Applications of theorem proving for securing the windows…

56 min
IMMI, from concept to reality
The Icelandic Modern Media Initiative and our need for a…
72 min
Lightning Talks - Day 3
where is my community?
24 min
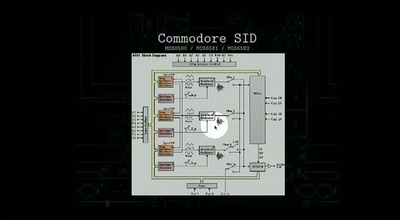
DIY synthesizers and sound generators
Where does the sound come from?
57 min
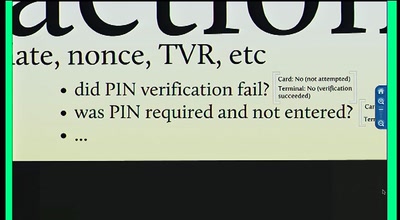
Chip and PIN is Broken
Vulnerabilities in the EMV Protocol
25 min
SIP home gateways under fire
Source routing attacks applied to SIP
58 min