Search for ">Y<" returned 10976 results
59 min
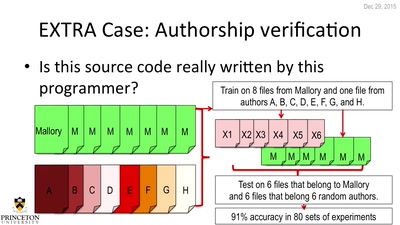
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
57 min
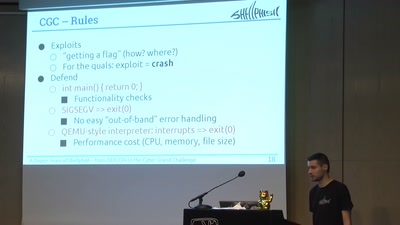
A Dozen Years of Shellphish
From DEFCON to the DARPA Cyber Grand Challenge
60 min
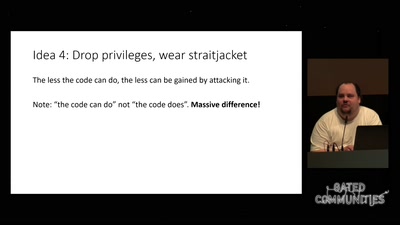
Check your privileges!
How to drop more of your privileges to reduce attack…
57 min
"Fluxus cannot save the world."
What hacking has to do with avantgarde art of the 1960ies…
55 min
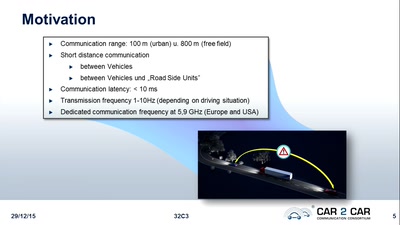
Graphs, Drones & Phones
The role of social-graphs for Drones in the War on Terror.
61 min
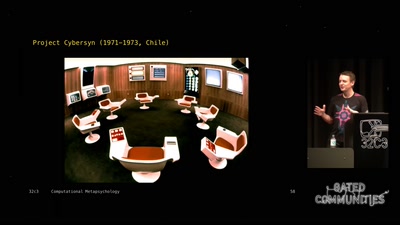
Computational Meta-Psychology
An Artificial Intelligence exploration into the creation of…
60 min
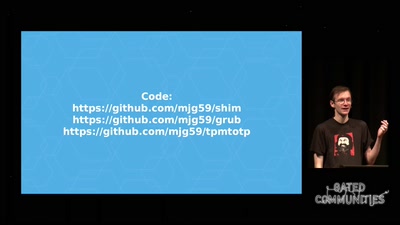
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…
60 min
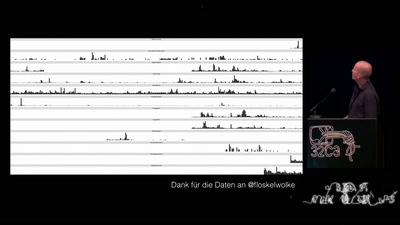
„Nach bestem Wissen und Gewissen“ – Floskeln in der Politik
Politische Phrasologie – warum man aus dem ganzen Zeug, das…
128 min
Methodisch inkorrekt!
Die Wissenschaftsgala vom 32C3
63 min
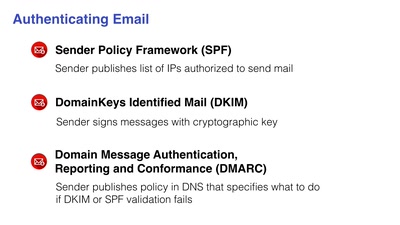
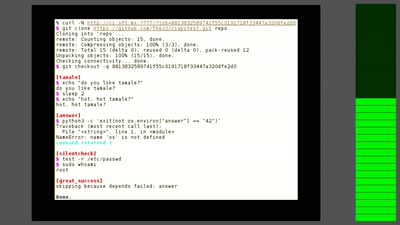
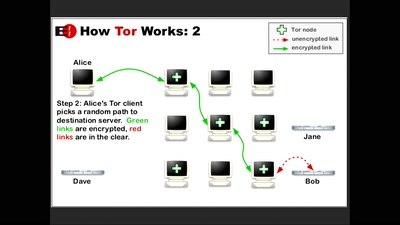
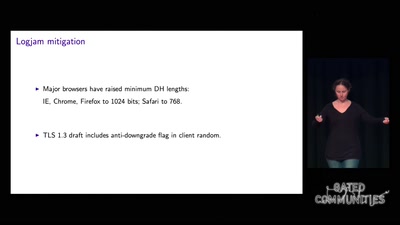
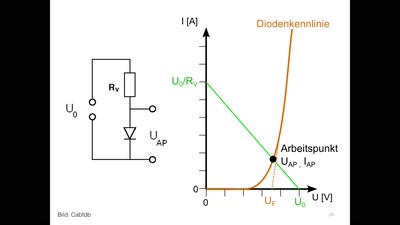
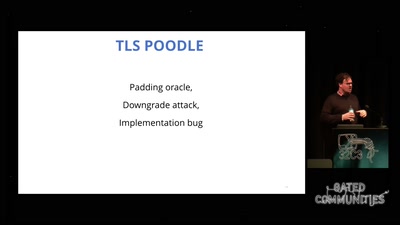
goto fail;
exploring two decades of transport layer insecurity
43 min
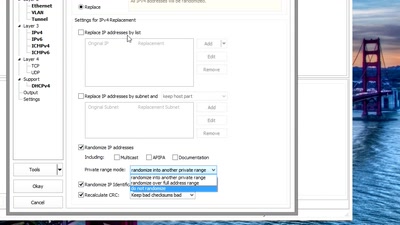
Sanitizing PCAPs
Fun and games until someone uses IPv6 or TCP
60 min
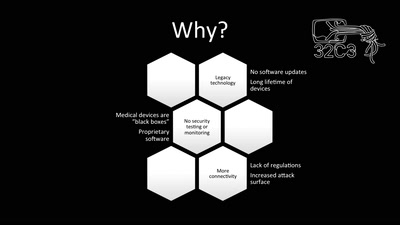
Unpatchable
Living with a vulnerable implanted device
56 min
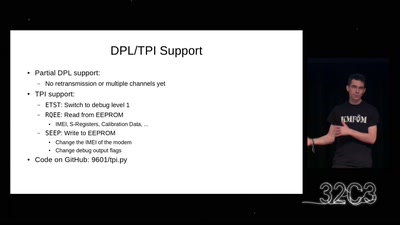
Iridium Update
more than just pagers
49 min
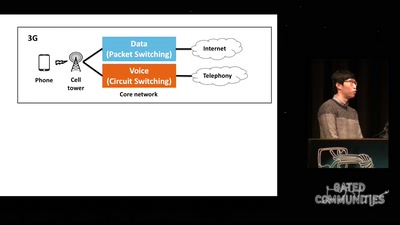
Dissecting VoLTE
Exploiting Free Data Channels and Security Problems

61 min