Search for "*m" returned 12091 results
52 min
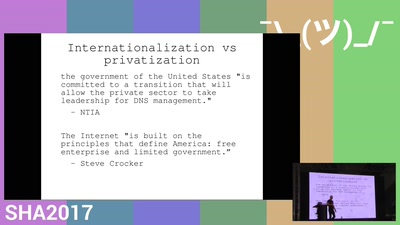
Human Rights and Internet Infrastructure
standard or substandard?
50 min
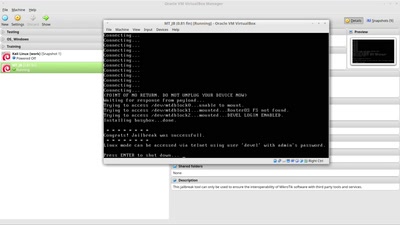
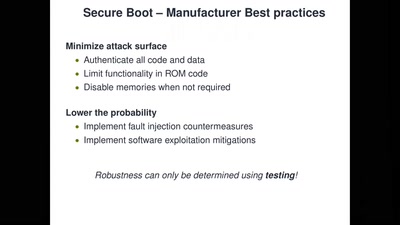
Bypassing Secure Boot using Fault Injection
Bypassing Secure Boot using Fault Injection
61 min
Human body as an electric IO system
Hacking your brain, and other body parts. Debunking myths…

38 min
Hardware games
How to build alternative controllers

32 min
Cryptokids
empower kids and provide tools for them to be more secure…

28 min
Exploiting The North American Railways
Modern Day American Hobo-ism
64 min
Fermentation Mobile
experimental, educational and commercial fermentation…
51 min
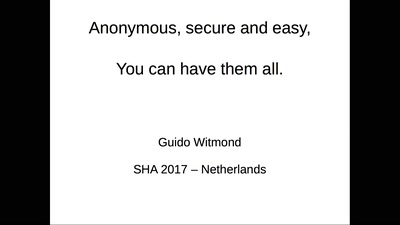
Anonymous, secure and easy. You can have them all.
An authentication protocol that offers security, privacy…
18 min
Malware: From your text editor, to the United States Government's Lab
How Universities in the US collaborate with the United…
39 min
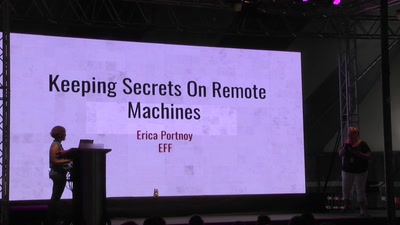
My Safe In Your House
Keeping Secrets On Remote Machines
46 min
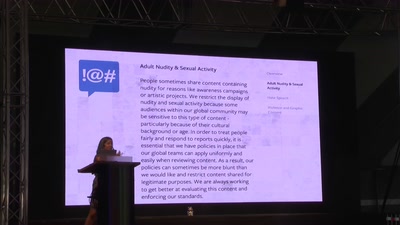
SHOULD I STAY OR SHOULD I GO?
THE ALGORITHMIC PUBLIC SPHERE AND YOU
47 min
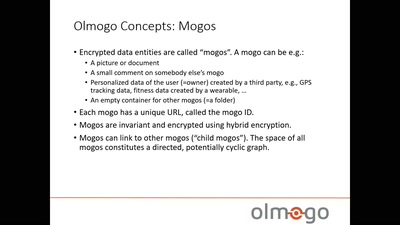
Olmogo - because it's your data!
A cryptographically secure social network platform
40 min
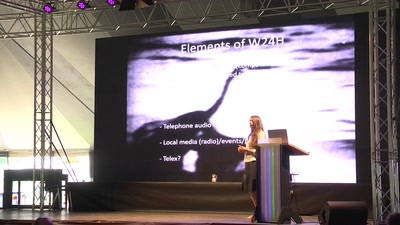
The World in 24 Hours Revisited
How to re-enact a 1982 network art performance

59 min
Developments in Coordinated Vulnerability Disclosure
The government is here to help
63 min